
AVAILABLE NOW
http://www.damballa.com/solutions/downloads.php
http://www.networkworld.com/community/node/58829
The biggest cloud on the planet is owned by … the crooks
by Robert Mullins / Mar 22 2010
Who’s got the biggest cloud in the tech universe? Google? Pretty big, but no. Amazon? Lots and lots of servers, but not even close. Microsoft? They’re just getting started. Household names all, but their capacity pales to that of the biggest cloud on the planet, the network of computers controlled by the Conficker computer worm. Conficker controls 6.4 million computer systems in 230 countries at 230 top level domains globally, more than 18 million CPUs and 28 terabits per second of bandwidth, said Rodney Joffe, senior vice president and senior technologist at the infrastructure services firm Neustar. The biggest cloud on the planet is controlled by a vast criminal enterprise that uses that botnet to send spam, hack computers, spread malware and steal personal information and money, Joffe said. In other words, the cloud is mobbed up.
Joffe explained how Conficker meets the definition of a cloud service provider in a presentation at the Cloud Connect conference held last week in Santa Clara, Calif. Like legitimate cloud vendors, Conficker is available for rent and is just about anywhere in the world a user would want their cloud to be based. Users can choose the amount of bandwidth they want, the kind of operating system they want to use and more. Customers have a variety of options for what services to put in the Conficker cloud, be it a denial-of-service attack, spam distribution or data exfiltration.
Joffe said Conficker has not been as active as it once was, but is still a threat. The last reported attack was in February on the network of the Manchester, UK, police department [6]. Joffe said the last major Conficker attack was in April 2009. Conficker is much more competitive than those legit vendors in many ways, Joffe continued. It has much more experience, dating back to 1998, has a larger footprint and unlimited new resources as it spreads malware far and wide to take over more computers. “And there are no costs. And there are no moral, ethical or legal constraints,” Joffe said, to chuckles from the audience. After all, the criminals stole their computing capacity from someone else.
By the way, the biggest legitimate cloud provider is Google, based on Joffe’s information, made up of 500,000 systems, 1 million CPUs and 1,500 gigabits per second (Gbps) of bandwdith. Amazon comes in second with 160,000 systems, 320,000 CPUs and 400 Gbps of bandwidth, while Rackspace offers 65,000 systems, 130,000 CPUs and 300 Gbps. Joffe described the vastness of the Conficker cloud to make a point that companies need to do their homework as they decide to sign up for cloud computing services as well as how to run their own IT systems. They should study up on botnets like Conficker, protect their own infrastructure and applications and assume they’ll someday be a target of botnets because “they’re great learners,” he said. And when a company does subscribe to a cloud computing service, make sure the provider is aware of your general “behavior,” he said, such as usual patterns of compute cycles and other signs. They have a name for cloud clients whose behavior becomes abnormal, meaning they could have been compromised, Joffe said: black clouds.
NEW BUSINESS MODELS
http://ha.ckers.org/blog/20100314/conversations-with-a-blackhat/
http://threatpost.com/en_us/blogs/future-botnets-031510
The Future of Botnets
by Dennis Fisher / March 15, 2010
A lot of people in the security industry are paid to think like attackers: pen testers, security consultants, software security experts. But some of these people have never met an actual black hat, so much of their work is necessarily based on what they think attackers might do in a given situation. Considering the stakes in today’s security game, gleaning intelligence from professional attackers is an invaluable experience for researchers on the other side of the ball. Robert Hansen, a security researcher and CEO of SecTheory, has been doing just that in recent months, having a series of off-the-record conversations with spammers and malicious hackers in an effort to gain insight into their tactics, mindset and motivation.
In a blog post describing one such conversation, Hansen says that the attacker was lamenting the difficulty of executing targeted attacks against machines in high-value networks. Security systems are doing a fairly good job of making life difficult for him.
“HeŌĆÖs not the type to hack randomly, heŌĆÖs only interested in targeted attacks with big payouts. Sure, if you really work at it for days or weeks youŌĆÖll get in, almost always, but itŌĆÖs not like it used to be where youŌĆÖd just run a handful of basic tests and you were guaranteed to break in. The risk is that now when he sends his mules to go cash out, thereŌĆÖs a chance theyŌĆÖll get nailed. Well, the more I thought about it the more I thought that this is a very solvable problem for bad guys. There are already other types of bad guys who do things like spam, steal credentials and DDoS. For that to work they need a botnet with thousands or millions of machines. The chances of a million machine botnet having compromised at least one machine within a target of interest is relatively high.”
Hansen’s solution to the hacker’s problem provides a glimpse into a busines model we might see in the not-too-distant future. It’s an evolutionary version of the botnet-for-hire or malware-as-a-service model that’s taken off in recent years. In Hansen’s model, an attacker looking to infiltrate a specific network would not spend weeks throwing resources against machines in that network, looking for a weak spot and potentially raising the suspicion of the company’s security team.
Instead, he would contact a botmaster and give him a laundry list of the machines or IP addresses he’s interested in compromising. If the botmaster already has his hooks into the network, the customer could then buy access directly into the network rather than spending his own time and resources trying to get in.
“This tactic reminds me a little of the movie Wall Street. You have a failing company (in this case a botnet that will probably only last a year or two). If the company continues on itŌĆÖs course itŌĆÖll make a pretty good amount of money, but nowhere near as much as if the owners break up the company into pieces and sell them off one by one to the interested parties. Kind of an interesting/scary thought, but it could easily be used to avoid the cost and danger of individual exploitation against a company for a hacker interested in target attacks. Rather, a brokerage for commodities (bots that come from interesting IPs/domains) could be created and used to sell off the individual nodes.”
This model makes sense on a number of levels and may well have been implemented already. The value of a large botnet for executing DDoS attacks or extracting valuable data from the compromised machines could be multiplied hundreds or thousands of times using this model.

Storm botnet visualization
BOTNET ECONOMICS
http://www.icsi.berkeley.edu/pubs/networking/2008-ccs-spamalytics.pdf
Researchers hijack botnet for spam study
by John Leyden / 10th November 2008
Pharmacy-touting spammers can turn a decent return on response rates as low as one in 12 million, far lower than previously thought. So say security researchers at the University of California, San Diego and UC Berkeley, who infiltrated the control system of the Storm botnet to research the economics of spam. At the peak of its activity in September last year, yhe Storm network of compromised PCs spewed out up to one in five junk mail messages.
Over 26 days this spring, the Storm botnet generated 350 million junk mail messages promoting the researchers’ dummy pharmacy sites. The virtual storefronts established by the researchers only mimicked the penis pill pushing sites typically spamvertised using the Storm botnet. The dummy sites worked up until the point of purchase. They returned a site error message after would-be customers tried to pay for goods in their shopping cart but before prompting for credit card details or shipping information. In this way the researchers avoided the collection of any personal data.
The huge volume of junk mail the researchers redirected generated just 28 attempted sales – all but one for male enhancements products – with an average “purchase” of just under $100 or $2,731 in total. The researchers reckon one in four of the emails they subverted made it past spam filters and conclude that this level of return only makes sense if the unknown bot herders have set themselves up as affiliates of pharmacy sites. Renting a botnet, or hiring a third-party to send spam, with these low levels of return would not make economic sense, the Californian academics conclude.
All above board
At first sight it might appear that the researchers were sending spam to study spam. But the set-up is more complicated than that and above board, according to security experts we asked to comment of the ethical implications of the exercise. “The researchers didn’t send any spam themselves, but instead subverted part of the Storm botnet into sending a spam template which pointed to their own innocuous website rather than the one that the real spammers wanted people to arrive at,” explained Graham Cluley, senior technology consultant at net security firm Sophos. “As such – no extra spam was sent, but more of the spam which was sent was non-dangerous,” he added.
The Californian academics reckon they misdirected the activity of about 1.5 per cent of the compromised worker bots than made up the zombie drones in the Storm worm botnet. Based on this estimate, and their own findings during the experiment on sales conversion, the researchers estimate the Storm worm generated $7,000 or $9,500 in pharmacy sales a day during the time of the experiment.
Separately ,the researchers looked at the percentage of users who clicked on the type of link that normally leads to websites harboring the Trojan downloader code that turns vulnerable Windows PCs into Storm worm zombie drones. They hijacked Storm worm email lures and discovered one in ten people who received the email clicked onto what would normally have been dodgy domains. Based on circumventing 120 million malware-propagating messages, that it might be possible to infect between 3,500 to 8,000 drones a year, the researchers say.
CONFICKER: ABANDONED, SLEEPING OR DEAD?
http://www.pcworld.com/article/162662/are_you_infected_a_smart_and_simple_test.html
http://www.pcworld.com/article/157876/protecting_against_the_rampant_conficker_worm.html
http://www.confickerworkinggroup.org/wiki/pmwiki.php/ANY/RepairTools
http://www.confickerworkinggroup.org/wiki/pmwiki.php/ANY/InfectionTracking
http://www.networkworld.com/news/2009/103009-after-one-year-conficker-infects.html
After one year, Conficker infects over 7 million computers
by Robert McMillan / October 30, 2009
The Conficker worm has passed a dubious milestone. It has now infected more than 7 million [m] computers, security experts estimate. On Thursday, researchers at the volunteer-run Shadowserver Foundation logged computers from more than 7 million unique IP addresses, all infected by the known variants of Conficker.
How to fight Conficker
They have been able to keep track of Conficker infections by cracking the algorithm the worm uses to look for instructions on the Internet and placing their own “sinkhole” servers on the Internet domains it is programmed to visit. Conficker has several ways of receiving instructions, so the bad guys have still been able to control PCs, but the sinkhole servers give researchers a good idea how many machines are infected. Although Conficker is probably the computer worm most known about, PCs continue to get infected by it, said Andre DiMino, co-founder of The Shadowserver Foundation. “The trend is definitely increasing and breaking 7 million is pretty much of a landmark event,” he said.
Conficker first caught the attention of security experts in November 2008 and received widespread media attention in early 2009. It has proved remarkably resilient and adept at re-infecting systems even after being removed. The worm is very common in, for instance, China and Brazil. Members of the Conficker Working Group, an industry coalition set up last year to deal with the worm, suspect that many of the infected PCs are running bootlegged copies of Microsoft Windows, and are therefore unable to download the patches or Microsoft’s Malicious Software Removal Tool, which could remove the infection.
Despite its size, Conficker has rarely been used by the criminals who control it. Why it hasn’t been used more is a bit of a mystery. Some members of the Conficker Working Group believe that Conficker’s author may be reluctant to attract more attention, given the worm’s overwhelming success at infecting computers. “The only thing I can guess at is the person who created this is scared,” said Eric Sites, chief technology officer with Sunbelt Software and a member of the working group. “This thing has cost so many companies and people money to get fixed, if they ever find the guys who did this, they’re going away for a long time.”
IT staffers often discover a Conficker infection when a user is suddenly unable to log into a computer. That happens because infected machines try to connect to other computers on the network and guess their passwords, trying so many times that they are eventually locked out of the network. But the cost of the worm would be even greater if Conficker were to be used for a distributed denial of service attack, for instance. “This is certainly a botnet that could be weaponized,” DeMinno said. “When you have a net of this magnitude, the sky’s the limit in terms of what could be done.”

Map of infected users, 2009
COMMAND & CONTROL
http://www.darkreading.com/vulnerability_management/security/attacks/showArticle.jhtml?articleID=224201115
Still 6.5 million machines infected, and worm continues to spread
by Kelly Jackson Higgins / April 1, 2010
After over a year of waiting for the sleeping giant Conficker botnet to come to life, some security researchers are now starting to think it may just be dead rather than dormant: they say the original creators of the Conficker botnet appear to have abandoned ship, leaving the worm to merely spread on its own via unpatched Windows machines. “This botnet is dead in the water,” says Vincent Weafer, vice president of Symantec Security Response. “At this point, we think the organization [behind it] has effectively abandoned it” since last May, he says. But that doesn’t mean Conficker still doesn’t pose a threat: another group could take control of the 6.5 million machines worldwide still infected with the Conficker worm, Weafer says. “It is possible someone could come along and try to take it over. We do see cross-infection all the time.”
Conficker’s original operators couldn’t activate the high-profile botnet without attracting too much attention, experts say, which may be why it’s been dormant for so long. The Conficker Working Group, formed in February of 2009 and led by Microsoft, has been successful in neutralizing the botnet, closely tracking its movements, and in leading the cleanup efforts. Gunter Ollmann, vice president of research at Damballa, says Conficker appears to be dead from a criminal operations perspective: “We still see frequent outbreaks within enterprise networks, typically through infected laptop users or infected USB memory keys, but are not seeing any criminal C&C activity,” Ollmann says. Meanwhile, Andre’ DiMino, director of the Shadowserver Foundation, says he doesn’t think Conficker’s operators have completely abandoned the botnet, however. “With a botnet that large and geographically distributed, it is a very good asset to maintain. While it remains dormant, the potential for its use, rental, or reconnaissance remains,” DiMino says.
With the crypto algorithms built into Conficker, it would be unlikely for another group to hijack the botnet, he notes. “However, it’s important to keep in mind that the Conficker drones are vulnerable machines that do not receive AV or OS updates. That’s why it’s still a high priority that Conficker drone remediation continues and the public remains aware of the threat,” DiMino says. Both DiMino and Weafer agree that Conficker’s creators could merely start all over again and build another botnet. “I wouldn’t put it past the current Conficker herders to look to build another botnet and adopt some of their own lessons learned,” DiMino says. That strategy would be much easier for them than activating Conficker, Symantec’s Weafer says.
It was exactly one year ago today — April Fool’s Day — that the security industry waited for Conficker to pull the trigger on its payload. But nothing happened, nor has much changed in the past year except for the steady stream of unpatched machines getting infected by the worm. Thus, fears that the botnet, which at one time ballooned to some 8 million machines, would be used for massive distributed denial-of-service (DDoS) attacks or other nefarious activities, have for the most part subsided.
Other researchers say Conficker is far from dead today: “Conficker is alive and well and still very active in attempting to spread. It is more dormant in the fact that there are no new payloads getting pushed down to Conficker because of the actions taken by various folks in the Internet and research communities,” says Marc Maiffret, chief security architect at FireEye. “The ability to control Conficker still remains, and it is something we continue to keep a watchful eye on, should it start to awaken again. I would definitely not call it down for the count.” Maiffret says Conficker’s authors can still control the botnet: “I don’t think that has gone away. They just have their foot off the gas,” he says. But Symantec’s Weafer says Conficker’s high profile and size make it “too toxic” for its operators to fully activate it. “There are too many people watching it,” he says, and if Conficker’s creators were to power it up, it could blow their cover, he says.
And remaining off the radar is something the Conficker creators have been able to avoid thus far. Microsoft’s $250,000 bounty for information that leads to the arrest and conviction of the people responsible for Conficker has yet to be awarded. “The investigation is currently ongoing, seeking those responsible for illegally launching the Conficker malicious code on the Internet,” said Jerry Bryant, group manager, for response communications at Microsoft, in a statement. Bryant noted that the CWG, security researchers, ICANN, and domain operators have teamed up to disable a “significant number” of domains used by Conficker, therefore disrupting the worm and preventing some attacks.
SHADOWSERVER FOUNDATION
http://www.shadowserver.org/wiki/pmwiki.php/Information/Botnets
http://www.shadowserver.org/wiki/pmwiki.php/Information/BotnetDetection
http://www.shadowserver.org/wiki/pmwiki.php/Stats/BotnetMaps
http://www.shadowserver.org/wiki/pmwiki.php/Stats/BotCounts
http://www.shadowserver.org/wiki/pmwiki.php/Information/Links
BOTNET WARS
http://www.symantec.com/connect/blogs/spyeye-bot-versus-zeus-bot
http://www.computerworld.com/s/article/9154618/New_Russian_botnet_tries_to_kill_rival
New Russian botnet tries to kill rival
‘Kill Zeus’ removes rival software from PC
by Robert McMillan / February 9, 2010
An upstart Trojan horse program has decided to take on its much-larger rival by stealing data and then removing the malicious program from infected computers. Security researchers say that the relatively unknown [Spy Eye toolkit] added this functionality just a few days ago in a bid to displace its larger rival, known as Zeus. The feature, called “Kill Zeus,” apparently removes the Zeus software from the victim’s PC, giving Spy Eye exclusive access to usernames and passwords.
Zeus and Spy Eye are both Trojan-making toolkits, designed to give criminals an easy way to set up their own “botnet” networks of password-stealing programs. These programs emerged as a major problem in 2009, with the U.S. Federal Bureau of Investigation estimating last October that they have caused $100 million in losses. Trojans such as Zeus and Spy Eye steal online banking credentials. This information is then used to empty bank accounts by transferring funds to so-called money mules — U.S. residents with bank accounts — who then move the cash out of the country.
Sensing an opportunity, a number of similar Trojans have emerged recently, including Filon, Clod and [Bugat], which was discovered just last month. Spy Eye popped up in Russian cybercrime forums in December, according to Symantec Senior Research Manager Ben Greenbaum. With its “Kill Zeus” option, Spy Eye is the most aggressive crimeware, however. The software can also steal data as it is transferred back to a Zeus command-and-control server, said Kevin Stevens, a researcher with SecureWorks. “This author knows that Zeus has a pretty good market, and he’s looking to cut in,” he said.
Turf wars are nothing new to cybercriminals. Two years ago a malicious program called Storm Worm began attacking servers controlled by a rival known as Srizbi. And a few years before that, the authors of the Netsky worm programmed their software to remove rival programs Bagle and MyDoom. Spy Eye sells for about $500 on the black market, about one-fifth the price of premium versions of Zeus. To date, it has not been spotted on many PCs, however. Still, the Trojan is being developed quickly and has a growing list of features, Greenbaum said. It can, for example, steal cached password information that is automatically filled in by the browser, and back itself up via e-mail. “This is interesting in its potential, but it’s not currently a widespread threat at all,” he said.
RESEARCHERS HIJACK TORPIG
http://www.cs.ucsb.edu/~seclab/projects/torpig/torpig.pdf
http://www.darkreading.com/security/client/showArticle.jhtml?articleID=217201422
http://www.scmagazineus.com/researchers-hijack-control-of-torpig-botnet/article/136207/
Researchers hijack control of Torpig botnet
by Chuck Miller / May 05 2009
A group of researchers at the University of California, Santa Barbara, have infiltrated the Torpig botnet, which was found to be in control of hundreds of thousands of computers that were volunteering gigabytes of sensitive information. The eight researchers, who actually took over the botnet for 10 days by seizing its command-and-control (C&C) channel, observed 180,000 infections and recorded more than 70 gigabytes of harvested data before losing control. In a paper reporting the results of their work, the researchers said that at one point data was being uploaded to them every 20 minutes.
Torpig is an advanced piece of crimeware, typically associated with bank account and credit card theft, according to the researchers, who work in the university’s Department of Computer Science. Torpig uses a C&C technique that has also been adapted by the Conficker botmasters. That is, each infected bot periodically generates a list of domains to contact. The first server that sends a valid C&C reply is considered genuine.
The researchers used information about the Torpig domain generation algorithm to quickly register domains that the infected bots would contact ŌĆō before the bot herders did. Then, when provided a valid response, the infected bots accepted the researcher’s servers as genuine. Among their findings, the researchers learned that typical evaluations of botnet sizes, based on the count of distinct IPs, might be overestimated. ŌĆ£We found that, in our case, the number of unique IPs was one order of magnitude larger than the actual number of infected hosts,ŌĆØ they wrote in the report.
They also said that the victims of botnets are generally users with poorly maintained machines. Victims invariably choose easily guessed passwords to protect access to sensitive sites. ŌĆ£This is evidence that the malware problem is fundamentally a cultural problem,ŌĆØ they wrote. ŌĆ£Even though people are educated and understand concepts such as physical security and the necessary maintenance of a car, they do not understand the consequences of irresponsible behavior when using a computer.ŌĆØ
In addition, the researchers said that interacting with registrars, hosting facilities, victim institutions, and law enforcement is a complicated process. ŌĆ£However, a few simple rules of behavior imposed by the U.S. government would go a long way toward preventing malicious internet behavior,ŌĆØ they wrote. ŌĆ£Even though botnets are a global problem, the United States could effectively enforce rules of behavior that might make it harder for botmasters to use the nation’s cyberinfrastructure with impunity.ŌĆØ
CONTACT
Giovanni Vigna
http://www.cs.ucsb.edu/~seclab/
http://www.cs.ucsb.edu/~vigna/
email : vigna [at] cs.ucsb [dot] edu
AND THEN MEBROOT
http://www.technologyreview.com/computing/23566/
Researchers Hijack a Drive-By Botnet
by Robert Lemos / October 02, 2009
By infiltrating a criminal computer network aimed at infecting visitors to legitimate websites, university researchers have gained firsthand insight into the scale and scope of so-called “drive-by downloading.” They found more than 6,500 websites hosting malicious code that redirected nearly 340,000 visitors to malicious sites. Drive-by downloading involves hacking into a legitimate site to covertly install malicious software on visitors’ machines or redirect them to another site.
In an unpublished paper, researchers at the University of California at Santa Barbara describe a four-month study in which they connected their servers to a collection of compromised computers known as the Mebroot botnet. Among their findings, the researchers discovered that, while the seedier sites on the Internet–those hosting porn and illegal downloads–were most effective at redirecting users to a malicious download site, business sites were more common among the compromised referrers. “Once upon a time, you thought that if you did not browse porn, you would be safe,” says Giovanni Vigna, a UCSB professor of computer science and one of the paper’s authors. “But staying away from the seedy places on the Internet is no longer an assurance of staying safe.”
First discovered by researchers in late 2007, the Mebroot network uses compromised websites to redirect visitors to centralized download servers that attempt to infect the victim’s computer. The malicious software, named for its tactic of infecting a Windows computer’s master boot record (MBR), shows signs of professional programming, including a rapid cycle of debugging, researchers say. “It is definitely one of the most advanced and professional botnets out there,” says Kimmo Kasslin, director of security response for antivirus firm F-Secure, which is based in Helsinki, Finland.
Using a variety of methods, the criminals behind Mebroot infect legitimate Web servers with Javascript code. The code redirects visitors to a different Internet domain, which changes every day, and where a malicious server attempts to compromise their computer with a program that provides the botnet’s owners with remote control over that machine. The custom domain generation technique is a relatively sophisticated way to foil attempts to permanently shut down the network, the researchers say. Older drive-by download schemes have redirected victims to a hard-coded Web address. Rather than a static address, the Javascript used by Mebroot generates a new address every day, similar to the domain algorithm used by another computer pest called Conficker. However, because the algorithm relies on known inputs–namely the date–domains can be precomputed, aiding the defenders. The Conficker Working Group, for example, attempted to reserve future domains at least a month in advance.
During the four months the researchers studied Mebroot, the infection network used three different domain-generation algorithms, two of which only used the day’s date as an input. The last variant, however, adds a variable that cannot be easily guessed well in advance: The second characters of the day’s most popular search term on Twitter. “They (Mebroot’s creators) used a variable that was not in control of the bad guys or the good guys,” says Marco Cova, a UCSB student and a coauthor of the paper. After they reverse-engineered the domain-generation algorithm, the researchers temporarily hijacked Mebroot by mirroring the steps the compromised websites take to calculate the current day’s domain and registering those domains themselves. But the researchers noticed that when they registered a domain for their sinkhole servers, the Mebroot gang would react by registering future domains faster.
The researchers were also able to profile the typical victim of the network. Almost 64 percent of the visitors redirected to the researchers’ servers were running Windows XP, while 23 percent were using Windows Vista. The next two most popular operating systems were Mac OS X 10.4 “Tiger” and Mac OS X 10.5 “Leopard,” which accounted for 6.4 percent of all visitors. The researchers never compromised visitors’ systems. But they were able to find evidence that they had been infected by analyzing two kinds of information sent over the network. One suggested that 6.5 percent of visitors were infected with malware. The other indicated that 13.3. percent of systems had been modified by malicious or unwanted files. Moreover, more than half–about 54 percent–were running some sort of antivirus software. About 12 percent of those running the security software were also infected by malware, the researchers found.
The researchers also discovered that nearly 70 percent of those redirected by Mebroot–as classified by Internet address–were vulnerable to one of almost 40 vulnerabilities regularly used by the most popular infection toolkits designed to compromise computer systems. About half that number were vulnerable to the six specific vulnerabilities used by the Mebroot toolkit. The research suggests that users need to update more often, says UCSB’s Vigna. “Patches are very good at reducing the exposure of the end users, but users are not very good at updating their system,” he says.
BOTMASTER PROFILE
http://www.techradar.com/news/internet/botnets-who-s-behind-them-and-why–644070
Cisco boffins infiltrate a botnet to find out about online crime
by Jon Thompson / October 26th
Poor education, a criminal record and a dislike of authority can all turn programmers bad. That’s the finding of Cisco researchers who posed as botmasters to enter the world of online crime. “I wanna do what I wanna do, whenever I want,” one botmaster told the researchers. By posing online as a rogue programmer, the researchers got him to reveal how he spams thousands of instant messenger users with enticements to install infected utilities.
For every 10,000 messages sent, “at least one per cent” will respond and become part of his botnet. The team, from Cisco’s Security Intelligence Operations unit, found that for botmasters, criminality is just a by-product of running a small business. The botmaster said he sold a 10,000-machine botnet for $800, but also claimed that selling off infected machines is relatively rare. He said that a friend made between $5,000 and $10,000 per week solely through renting out his botnet to phishing gangs.
Dumbing down
Today, those without the necessary computer skills can easily gain access to advanced tools for creating profitable, robust and secure botnets. Over the course of their online conversations, Cisco’s researchers learned of online marketplaces where the budding cybercriminal can buy everything he needs to set up a botnet. “The bot software is advertised much like any other software,” claims Cisco. “Anyone with basic computer experience is able to run one. It’s not necessary to understand the code, nor is there a need to understand networking.”
Following the money
Alex Constantinides is a director of UK-based online security consultancy MetaSec. “It just goes to show how these things have evolved,” he told us. “Originally, simply knocking servers off the net was the thing ŌĆō for fun. Then botnets became a blackmailing tool. Now they’re predominantly used for financial gain.” Janet Williams is a Deputy Assistant Commissioner with the Metropolitan Police Service, and she heads up the Police Central e-crime Unit (PCeU). Williams has just launched the ACPO e-crime Strategy, designed to help police forces pool their resources in response to e-crime. “This strategy is designed to assist law enforcement in building a response to this challenge,” says Williams. “We trust that by doing so we’ll enhance both industry and public confidence.”
Potential botmasters tend to fit a profile, so identifying them shouldn’t be difficult, as F-Secure’s Mikko Hypponen points out: “It’s often the people with the skills but without the opportunities,” he says. “Many of these online criminals are coming from developing countries. If you know how to code and are living in London ŌĆō great! You’ll get a job easy,” says Hypponen. “If you know how to code and are living in Siberia ŌĆō not so great.”
“The only real way to find the perpetrators, like traditional bank robberies, is to follow the money,” Roger Thompson, Chief Research Officer at AVG Technologies, told us. “However, even this becomes difficult as it involves multiple countries and there are many different layers and players.” The strongest psychological factor for many botmasters may simply be the excitement of breaking the law, as Hypponen concludes: “Some people would have the opportunities but still choose the dark sideŌĆ”” he says.
ZEUS FOUND IN AMAZON CLOUD
http://hackertarget.com/2009/06/amazon-cloud-service-brute-force/
http://developer.amazonwebservices.com/connect/entry.jspa?externalID=1233&categoryID=100
http://community.ca.com/blogs/securityadvisor/archive/2009/12/09/zeus-in-the-cloud.aspx
http://www.readwriteweb.com/archives/zeus-botnet-amazon-cloud-ec2.php
http://www.securityfocus.com/brief/1046
Zeus botnet finds hold in Amazon cloud / 2009-12-11
The cybercriminals behind the Zeus botnet used Amazon’s Elastic Computing Cloud (EC2) to host the central server used to control a portion of the compromised machines, security firm CA stated on Thursday. The company found that infected machines would contact a server hosted in Amazon’s cloud to download updates and additional functionality to any infected computer systems. The malicious software would then steal data and banking login credentials, Methusela Cebrian Ferrer, senior researcher at CA, said in a blog post. “The group behind this criminal activity is obviously doing it for financial gain ŌĆō stealing both your identity and your money,” Ferrer stated. “In this variant, we have learned how cloud on-demand — pay-as-you-use — offerings could be used to fuel such online cybercrimes.”
A number of security experts have predicted that cybercriminals will increasingly find uses for legitimate cloud services, such as Amazon’s Elastic Computing Cloud (EC2) and Google’s App Engine. This week, hacker Moxie Marlinspike kicked off a wireless password cracking service hosted in the cloud. The service, WPA Cracker, can compare the hash from a WiFi Protected Access network against 135 million possibilities in 40 minutes. A report from June alleged that brute force attacks against a secure shell service were coming from Amazon’s cloud service. The command-and-control server has since been removed from Amazon’s service, CA stated.

EARTHQUAKE SPAM
http://www.google.com/postini/index.html
http://googleenterprise.blogspot.com/2010/04/editors-note-spam-data-cited-in-this.html
Q1’10 spam & virus trends from Postini / April 14, 2010
Note: The spam data cited in this post is drawn from the network of Google email security and archiving services, powered by Postini, which processes more than 3 billion email connections per day in the course of providing email security to more than 50,000 businesses and 18 million business users.
In 2009, the security community started seeing diminishing returns from the takedown of malicious ISPs. After the ISP 3FN was taken down, spam levels rebounded in less than a month, and after Real Host went down, spam volumes recovered after only two days. In response, the anti-spam community turned its attention toward taking botnets offline instead. Toward the end of 2009, Mega-D, a top-10 botnet ŌĆō responsible for infecting more than 250,000 computers worldwide ŌĆō was severely crippled through a carefully orchestrated campaign designed to isolate the command-and-control servers spammers were using to support the botnet. In early 2010, security professionals, along with government agencies, successfully mounted a campaign against several more targets: major botnets such as Waledac, Mariposa, and Zeus were either shut down or had their operations significantly curtailed. However, this recent spate of botnet takedowns has not had a dramatic impact on spam levels. Although spam and virus levels did fall below Q4ŌĆÖ09 highs, reports from GoogleŌĆÖs global analytics show that spam levels held relatively steady over the course of Q1ŌĆÖ10. This suggests that thereŌĆÖs no shortage of botnets out there for spammers to use. If one botnet goes offline, spammers simply buy, rent, or deploy another, making it difficult for the anti-spam community to make significant inroads in the fight against spam with individual botnet takedowns.
Spam by the numbers
Overall, spam volume fell 12% from Q4ŌĆÖ09 to Q1ŌĆÖ10, which follows a trend of quarterly decreases in overall spam levels that started after the surge in Q2ŌĆÖ09. This may be attributed to some of the recent takedowns, but spam volume was still 6% higher this quarter than it was during the same period in 2009, and spam volume as a percentage of total email messages is holding steady. Recently, our data centers showed a 30% increase in the size of individual spam messages (measured in bytes) that occurred toward the end of March. This spike points to a resurgence of image spam, similar to what we reported in Q2ŌĆÖ09. This is likely due to the fact that reusing image templates makes it easier and faster for spammers to start new campaigns. As always, spammers tend to make use of predictable topics ŌĆō cheap pharmaceuticals, celebrity gossip, breaking news ŌĆō to encourage user clicks. In January, spammers hastened to exploit the Haiti earthquake crisis, sending pleas for donations that appeared to have been sent by reputable charitable organizations, politicians, and celebrities. The frequency and variety of post-earthquake spam illustrates an unpleasant reality: spammers will exploit any means ŌĆō even tragedies ŌĆō to accomplish their objectives.
Virus levels fall after Q4ŌĆÖ09 surge
During 2009, spam with attached viruses increased tenfold, with levels rising from 0.3% of total spam in the first half of the year to 3.7% in the second. Postini filters blocked more than 100 million virus-bearing messages per day during the worst of the attack. Since then, spam with attached viruses leveled off to around 1.1% in Q1ŌĆÖ10, and dropped as low as 0.7% in March. ItŌĆÖs good news that virus levels are currently trending down ŌĆō but Q1ŌĆÖ10 levels are still 12-fold higher than they were in Q1ŌĆÖ09. In fact, this virus surge may be part of the reason that there hasnŌĆÖt been a significant impact on spam volume after the recent takedown of major botnets. With a host of new machines now infected and part of a botnet, it is unlikely that there would be a dip in spam proliferation.
Benefits of security in the cloud
Although the botnets that distribute spam are mindless drones, the spammers that take advantage of these botnets are a highly active and adaptable group. This is evidenced by the varied techniques and tactics that they employ in an ongoing effort to evade spam filters and deliver messages to their targets. 2010 is likely to see more botnets taken offline, but the question remains ŌĆō will that have a long-term impact on spam volumes overall? So far in 2010, the effect has been limited, and the security community may begin to turn to other tactics that yield a more substantial impact on global spam volumes.
AFRICA GETS BROADBAND
http://intellibriefs.blogspot.com/2009/10/africa-home-of-worlds-largest-cyber.html
Africa – home of the worldŌĆÖs largest cyber pandemic / 10.04.2009
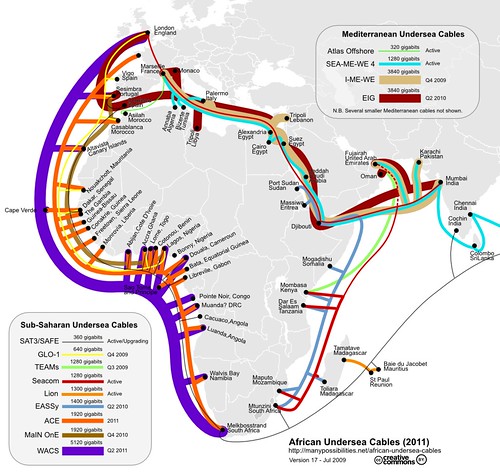
The above map illustrates the projected arrival of broadband service to Africa in 2010 and 2011 via undersea cables. ThatŌĆÖs the good news. The bad news, and the point of this post, is that Africa is home to about 100 million PCs, 80% of which are estimated to be infected with some kind of malware. This has occurred because the intense poverty throughout the continent has resulted in a pervasive distribution of pirated software and the inability to pay for Anti-Virus protection. Currently, most Internet access is via dial-up, but once broadband comes to Africa, all of those infected PCs will become an easy target for bot herders looking to build the next mega-botnet; Think about it. Almost a hundred million PCs with little to no AV protection connected to the Internet backbone via a super highway instead of a dirt path. What could a bad operator do with a botnet of that size? Pretty much anything he wants, including paralyzing an entire nationŌĆÖs networked infrastructure. ThatŌĆÖs all systems connected to the Internet, including power, water, communications, commerce, etc. If this were a public health risk, (a) it would never have been allowed to get this far out of hand, and (b) labs would be working around the clock to produce enough anti-virus serums to stop the pandemic in its tracks. If every infected PC in Africa were a person, this would rank as the second worst pandemic in the history of the world.
Today, botnets are a key asset for organized crime producing millions of dollars in revenue from a variety of malware schemes and a potentially potent weapon in Non-state geopolitical attacks against government Web sites. Simply put, AfricaŌĆÖs population of infected PCs is a significant emerging threat on an international scale and action must be taken to remedy it before those undersea cables go online. Since Microsoft Windows is the OS that we are talking about, it falls on Microsoft to do something about this problem. One good first step would be what MicrosoftŌĆÖs Paul Cooke discusses here – support pirated versions of Windows 7 with patches, etc. Keeping a machine up to date is one of the first steps in helping ensure that they remain reliable, compatible, and safe from threats when they are online. Some of the most famous incidents of malicious software infection have come after security updates were publicly available from Microsoft – Blaster, Zotob, Conficker and Sasser, just to name a few. Rest assured that we at Microsoft are committed to making sure that security updates are available to all of our users to help ensure a safe online experience for everyone. Just doing this for Windows 7 is not nearly enough. Microsoft needs to make this commitment for all Windows PCs or it becomes more of a PR stunt then a genuine effort to do the responsible thing. However, even if MSFT would commit to such a massive endeavor (and I donŌĆÖt believe that they would), it wouldnŌĆÖt be enough because of its reputation of issuing free updates to pirated PCs which, in turn, make them unusable. ThereŌĆÖs nothing wrong with that on principle, except that it has now established MSFT as untrustworthy (read the comments section of the above referenced Cooke quote to see what I mean). This means that other, independent agencies would have to vet the MSFT patches and security updates as not being disguised OS killers and then distribute them freely throughout Africa. AV firms like Symantec, McAfee, and others should also consider offering free subscriptions to their AV lines on a project by project basis. This one would certainly qualify for such an altruistic effort. Bottom line: if there isnŌĆÖt a global response to this threat before mid-2010, we will all come to regret the consequences, and global corporations who could afford to act and didnŌĆÖt, should be held accountable in the aftermath.
GHOSTNET
http://www.npr.org/templates/story/story.php?storyId=125907001
http://documents.scribd.com/docs/1jiyoq3c13a9a4udh2s7.pdf
http://www.cl.cam.ac.uk/techreports/UCAM-CL-TR-746.html
http://blogs.computerworld.com/ghostnet_spyware_china
http://arstechnica.com/security/news/2009/03/potential-chinese-cyberspy-network-runs-across-103-nations.ars
Chinese cyberespionage network runs across 103 nations
by Joel Hruska / March 30, 2009
The existence and operation of massive, coordinated, government-affiliated online espionage networks is typically the province of television or the silver screen, rather than the subject of research. In the real world, even a direct link between online and offline action (Russia’s invasion of Georgia and the simultaneous online attacks against that country are a good example) is not enough to automatically prove that the government behind the one is automatically behind the other. We’ve covered the rise of hacktivism previously on Ars; as more citizens come online, we’ll undoubtedly see more of this type of crowdsourced aggression in the future.
Researchers in Toronto, however, may have actually discovered and tracked a hacking effort that can be traced back to a foreign intelligence networkŌĆöChina’s, in this caseŌĆöover the past ten months. The team, which is affiliated with the Munk Centre for International Studies, has published an extensive report on the activities of what they dub GhostNet. Their investigation took place from June 2008 through March of 2009, and focused on allegations that the Chinese had engaged in systemic online espionage activities against the Tibetan community. GhostNet was spread through the use of a wide variety of Trojans, many of which were controlled through a program nicknamed gh0st RAT (Remote Access Tool).
The report can be read in one of two ways: either as a primer on the operation and capabilities of both the gh0st RAT tool and the GhostNet network, or as an intelligence document detailing (with some redactions) where GhostNet infections were found and, perhaps more importantly, where the espionage network’s C&C servers appear to be located. For the purposes of this discussion, we’re going to focus more on the sociopolitical implications of GhostNet and less on the technical details. It will have to suffice to say that gh0st RAT is apparently a complex and nasty bit of business that does not rely on the successful installation of one particular Trojan in order to operate.
Its various payloads appear to have been delivered using standard social engineering and/or spear phishing techniques. This could be seen as further proof that relatively simple attack vectors are sufficient to overwhelm the security training and/or antivirus software of high-level government institutions; many of the targets GhostNet infiltrated should never be susceptible to a gussied up version of a social engineering attack.
Just because you’re paranoid…
China has been accused of attacking a number of groups and institutions through the use of cyber espionage, a fact which already put it high on the research team’s “countries of interest” list. The team’s investigation ended up focused on Tibet in particular “because of the unprecedented access that we were granted to Tibetan institutions through one of our researchers and persistent allegations that confidential information on secure computers was somehow being compromised.” The report notes that the lead field researcher had a substantial history of working with the Tibetan community, and was able to secure access to “the private office of the Dalai Lama, the Tibetan Government-in-Exile (TGIE), and a number of Tibetan non-governmental organizations” (NGOs).
The group’s on-site research identified infected systems within the Office of His Holiness the Dalai Lama (OHHDL), the network of the TGIE, and the offices of a Tibetan NGO, TibTec. In the latter’s case, there was already anecdotal evidence of espionage within the Drewla Initiative Project. According to its description, “Drewla (‘connection’ in Tibetan) is an online outreach project…that employs Tibetan youth with Chinese language skills to chat with people in mainland China and in the diaspora, raising awareness about the Tibetan situation, sharing the Dala Lama’s teachings, and supplying information on how to circumvent…government censorship on the Internet.”
This is rather obviously the sort of project the Chinese government would be less than fond of. The anecdotal evidence we mentioned is given on page 29/53 of the PDF, which tells the story of a young member of Drewla who was returning to her family in Tibet after two years away. She was detained at the Nepalese/Tibetan border and held for two months. Accused of participating in the Drewla Initiative, “She denied having been politically active and insisted that she had gone to Dharamsala for studies. In response…the intelligence officers pulled out a dossier on her activitiies and presented her with full transcripts of her Internet chats over the years. They indicated that they were fully aware of, and were monitoring, the Drewla outreach initiative.”
…doesn’t mean they aren’t out to get you
GhostNet is extremely selective for a malware network. The Toronto researchers listed the following systems as ones they are highly confident have been compromised:
-ASEAN (Association of Southeast Asian Nations)
-Asian Development Bank
-Associated Press, UK
-Consulate General of Malaysia, Hong Kong
-Department of Foreign Affairs, Indonesia
-Department of Foreign Affairs, Philippines
-International Campaign for Tibet
-NATO (SHAPE HQ)
-Office of the Dalai Lama, India
-Russian Federal University Network, Russian Federation
-Students for a Free Tibet, US
-Taiwan Government Service network, Taiwan
-Tibetan Government in Exile, India
Ommitted from that list is any mention of the dozen-plus embassies believed to be infected across Southeast Asia or in other geographical areas of interest to China. As the authors themselves point out, there are plausible explanations for GhostNet that do not require it to be an espionage tool of the Chinese government, though they think that this explanation is both the most obvious and “the one in which the circumstantial evidence tilts the strongest.” The fact that the attack IPs examined resolve back “in at least several instances to Hainan Island, home of the Lingshui signals intelligence facility and the Third Technical Department of the People’s Liberation Army” definitely helps this case.
Alternatives must, however, be considered. These include the possibility that GhostNet is essentially a fluke, a deliberate creation of a foreign power other than China (but with a similar set of interests), or the creation of a group searching for information to sell at a profit. This last option is most plausible if we consider the likelihood that there are many GhostNets in operation around the world, each designed to monitor its own particular interests. As the authors note, they “can safely hypothesize that it [GhostNet] is neither the first nor the only one of its kind.”

INFORMATION WARFARE MONITOR
http://www.infowar-monitor.net/
http://www.infowar-monitor.net/research/
SON OF GHOSTNET
http://www.scribd.com/doc/29435784/SHADOWS-IN-THE-CLOUD-Investigating-Cyber-Espionage-2-0
http://arstechnica.com/security/news/2010/04/son-of-ghostnet-china-based-hacking-targets-india-government.ars
China-based hacking targets India government
by John Timmer / 4.7.2010
The people who uncovered GhostNet, an extensive cyber espionage network that targeted the Tibetan exile community, are back with a sequel. Starting with an infected machine that was found during that investigation, an international team of researchers has uncovered a completely separate network that primarily targeted the Indian government, and turned up some classified documents that had been obtained by the hackers. By reconstructing the network, the team was able to trace things back to the hacking community in Chengdu, China.
The work involved a collaboration between the Information Warfare Monitor and the Shadowserver Foundation, but, over the course of its work, involved dozens of other security groups and experts. It also benefitted from extensive cooperation with the Office of His Holiness the Dalai Lama, which had previously approached the security researchers in response to security lapses that unearthed GhostNet. The researchers take what they term a “fusion methodology,” which is basically a combination of fieldworkŌĆöstudying infected systems in situŌĆöwith standard security approaches.
The investigation grew out of GhostNet in two ways. As part of their efforts to help the Tibetan exile community secure its systems, the researchers were monitoring the network used by the OHHDL. As part of that monitoring, they uncovered an malware-infected machine that attempted to transfer documents to a control server. Separately, they found that most of the control servers identified through the GhostNet investigation were taken down after their report on it was released. As the domain registrations on these servers lapsed, the researchers grabbed them for themselves, and created what’s termed a DNS sinkhole, in which requests from compromised machines were directed to one under the researchers’ control, allowing a study of the command-and-control communications.
Over time, the authors were able to trace communications back and develop a reasonable picture of a computer espionage network that was separate from, but partially overlapped with, the GhostNet. It turns out that, just as hackers count on regular users having moments of carelessness, they suffer from the same problem, which allowed the researchers to view the complete list of infected systems four times, and obtain documents stolen by the hackers twice. In general, machines were compromised using low-tech methods, primarily via malware that travelled as Microsoft Office or PDF files, and used relatively well-known exploits. Once on a machine, however, the malware would communicate with a specific Yahoo Mail account, which allowed it to receive more sophisticated software via attachments, and alert the network to its identity.
The command-and-control network operated primarily through free webhosting services, many of them operating from within the US. As these systems came and went, various social networking servicesŌĆöGoogle and Baidu blogs, Twitter, etc.ŌĆöwere used to supply the infected systems with a list of alternate hosts. Fortunately for the researchers, at times when a lot of the free webhosts were taken out of action, the social networking updates revealed a core of servers that remained constant; these were exclusively hosted within China. The list of infected systems was pretty variable, and included US institutions like NYU and Honeywell, and at least one machine in China that the researchers think was used for testing the system. But the majority of infected machines were associated with India. Some of these were commercial, like the Times of India and the New Delhi rail station, but the list included Indian embassies and consulates.
The documents retrieved by the researchers include everything from information on missile systems being developed by India to a list of visas issued by Indian embassies. That latter item may have implications for NATO’s Afghanistan mission, since many of the officials from NATO countries travel via India. Several of these were marked classified or confidential, and some provided internal security evaluations in regions where India is dealing with armed insurgency.
Aside from the fact that the core of the network resides in China, there is some circumstantial evidence linking the network to the hacking community that exists in Chengdu. A blog that follows Chinese hacking activity independently identified the e-mail address used to register one of the domains that turned up as part of the new espionage network. The address turned up in several popular Chinese hacking forums, but also showed up in association with advertisements for apartment rentals in Chengdu. Several of the command-and-control e-mails sent to the Yahoo account also originated from computers in the region.
So, does that mean the Chinese government is behind the espionage? Chengdu is the site of an Army technical reconnaissance bureau, which would be consistent with direct involvement. But, it’s quite near Chongquing, a city with thriving criminal syndicates, and several of the servers were also traced to that city. Complicating matters further, China is one of the governments that has been accused of hiring digital privateers, private citizens that engage in hacking while remaining independent of the central government. The report notes that private citizens might engage in these activities under the expectation that the documents, once obtained, could be sold to the government, even if the government didn’t authorize the intrusions. In any case, the report’s authors mentioned that the Chinese CERT organization was cooperating with attempts to shut down the network.

