Peer-to-peer apps send information without involving distant servers or wireless carriers.
PHONE to PHONE MESH NETWORKS
http://www.technologyreview.com/news/516571/build-your-own-internet-with-mobile-mesh-networking/
http://www.engadget.com/2014/09/29/hong-kong-secure-messaging/
http://blogs.wsj.com/digits/2014/09/29/firechat-messaging-app-gains-users-during-hong-kong-protests/
http://www.npr.org/blogs/alltechconsidered/2014/09/29/352476454/how-hong-kong-protesters-are-connecting-without-cell-or-wi-fi-networks
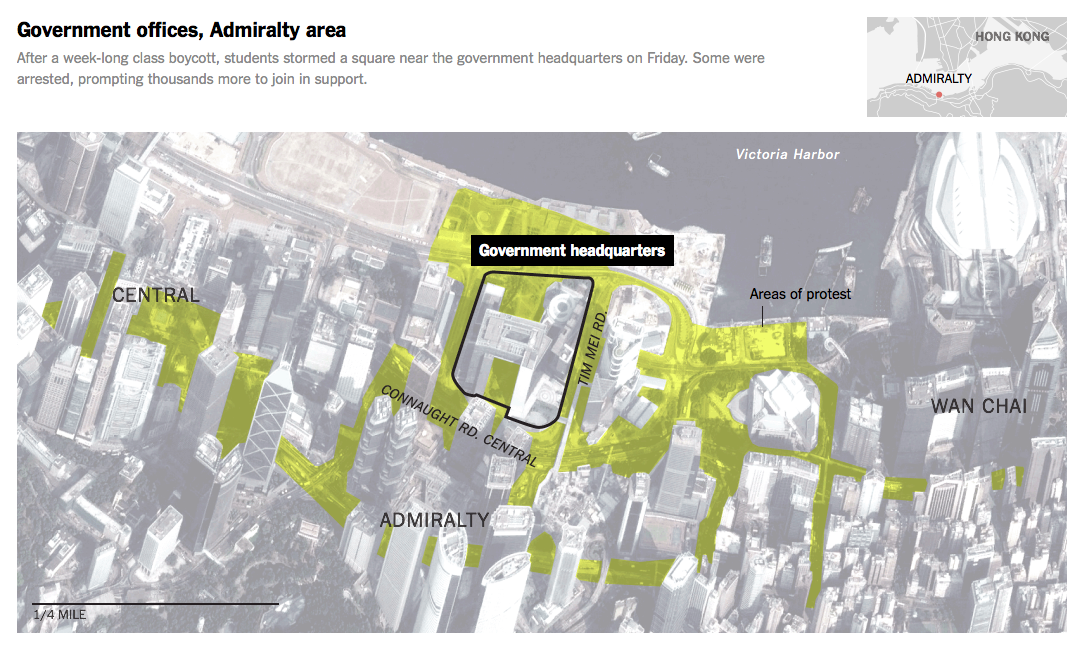
As throngs of pro-democracy protesters continue to organize in Hong Kong’s central business district, many of them are messaging one another through a network that doesn’t require cell towers or Wi-Fi nodes. They’re using an app called FireChat that launched in March and is underpinned by mesh networking, which lets phones unite to form a temporary Internet.
警方將會切斷中環金鐘灣仔一帶網絡,rthk已comfirm 未down firechat 快down 如果大家關注政總現場情況或會到政總, 請先到 AppStore 或 PlayStore 安裝及登入 FireChat…. http://t.co/7Pz9KbW6sr
— 黃之鋒 (@joshuawong1013) September 28, 2014
So far, mesh networks have proven themselves quite effective and quickly adopted during times of disaster or political unrest, as they don’t rely on existing cable and wireless networks. In Iraq, tens of thousands of people have downloaded FireChat as the government limits connectivity in an effort to curb ISIS communications. Protesters in Taiwan this spring turned to FireChat when cell signals were too weak and at times nonexistent.
And FireChat’s popularity is surging in Hong Kong. About 100,000 users downloaded the free FireChat app between Sunday morning and Monday morning, according to The Wall Street Journal. While there are no reports of cell-network outages so far, student leaders are recommending FireChat for fear authorities may shut off communications. Gizmodo explains why mesh networks can be critical during tense showdowns with governments:
“Mesh networks are an especially resilient tool because there’s no easy way for a government to shut them down. They can’t just block cell reception or a site address. Mesh networks are like Voldemort after he split his soul into horcruxes (only not evil). Destroying one part won’t kill it unless you destroy each point of access; someone would have to turn off Bluetooth on every phone using FireChat to completely break the connection. This hard-to-break connection isn’t super important for casual chats, but during tense political showdowns, it could be a lifeline.”
And as we have previously reported, Open Garden, the company that made FireChat and an Android mesh networking app also called Open Garden, has bigger ambitions for mesh networking:
“Once you build a mesh network … now you have a network that is resilient, self-healing, cannot be controlled by any central organization, cannot be shut down and is always working,” Christophe Daligault, Open Garden’s vice president for sales and marketing says. “I think that solves many other drawbacks or challenges of the mobile broadband Internet today.”
He says none of this would be possible without the rapid spread of smartphones, because that means no extra hardware is needed. “Each [phone] becomes a router and in a sense you’re growing the Internet — everyone who joins the mesh network creates an extension of the Internet,” Daligault says. “In a year or two from now, I think people won’t even remember that you had to be on Wi-Fi or get a cell signal to be able to communicate.”
without CELL PHONE RECEPTION
http://thinkprogress.org/world/2014/10/01/3574517/umbrella-protest-in-china/
http://www.newrepublic.com/article/119638/hong-kong-protests-behind-barricades
http://www.technologyreview.com/news/525921/the-latest-chat-app-for-iphone-needs-no-internet-connection/
The Latest Chat App for iPhone Needs No Internet Connection
by Tom Simonite / March 28, 2014
Mobile app stores are stuffed with messaging apps from WhatsApp to Tango and their many imitators. But FireChat, released last week for the iPhone, stands out. It’s the only one that can be used without cell-phone reception. FireChat makes use of a feature Apple introduced in the latest version of its iOS mobile software, iOS7, called multipeer connectivity. This feature allows phones to connect to one another directly using Bluetooth or Wi-Fi as an alternative to the Internet. If you’re using FireChat, its “nearby” chat room lets you exchange messages with other users within 100 feet without sending data via your cellular provider.

Micha Benoliel, CEO and cofounder of startup Open Garden, which made FireChat, says the app shows how smartphones can be set free from cellular networks. He hopes to enable many more Internet-optional apps with the upcoming release of software tools that will help developers build FireChat-style apps for iPhone, or for Android, Mac, and Windows devices. “This approach is very interesting for multiplayer gaming and all kinds of communication apps,” says Benoliel.
Anthony DiPasquale, a developer with consultancy Thoughtbot, says FireChat is the only app he’s aware of that’s been built to make use of multipeer connectivity, perhaps because the feature remains unfamiliar to most Apple developers. “I hope more people start to use it soon,” he says. “It’s an awesome framework with a lot of potential.

There is probably a great use for multipeer connectivity in every situation where there are people grouped together wanting to share some sort of information.” DiPasquale has dabbled in using multipeer connectivity himself, creating an experimental app that streams music from one device to several others nearby. The new feature of iOS7 currently only supports data moving directly from one device to another, and from one device to several others. However, Open Garden’s forthcoming software will extend the feature so that data can hop between two iPhones out of range of one another via intermediary devices.

That approach, known as mesh networking, is at the heart of several existing projects to create disaster-proof or community-controlled communications networks (see “Build Your Own Internet with Mobile Mesh Networking”). Apps built to exploit such device-to-device schemes can offer security and privacy benefits over those that rely on the Internet. For example, messages sent using FireChat to nearby devices don’t pass through any systems operated by either Open Garden or a wireless carrier (although they are broadcast to all FireChat users nearby).

That means the content of a message and metadata could not be harvested from a central communications hub by an attacker or government agency. “This method of communication is immune to firewalls like the ones installed in China and North Korea,” says Mattt Thompson, a software engineer who writes the iOS and Mac development blog NSHipster. Recent revelations about large-scale surveillance of online services and the constant litany of data breaches make this a good time for apps that don’t rely on central servers, he says. “As users become more mindful of the security and privacy implications of technologies they rely on, moving in the direction of local, ad-hoc networking makes a lot of sense.”

However, peer-to-peer and mesh networking apps also come with their own risks, since an eavesdropper could gain access to local traffic just by using a device within range. Open Garden’s main product is an app that allows Android devices to share their Internet connections (see “Could You Spare Some Internet Access?”).

However, Benoliel says that won’t be coming to the iPhone anytime soon because the feature that FireChat relies on cannot be used to share data connectivity. Peer-to-peer mobile communications and mesh networks could prove especially important in countries with minimal communications infrastructure. “You can see Google spending billions on fiber and balloons, but this is not going to solve the problem of ubiquitous mobile connectivity,” Benoliel says. He argues that the spread of cheap Android phones across the world will make mesh networking feasible. “We need to create small Internets that can function on their own and [then] connect them to the big Internet.”

LTE RADIO
http://chinaelectionsblog.net/hkfocus/?tag=benny-tai
http://www.scmp.com/news/hong-kong/article/1603506/how-occupy-central-leaders-lost-grip-protest
http://www.technologyreview.com/news/530996/future-smartphones-wont-need-cell-towers-to-connect/
Future LTE Radio Smartphones Won’t Need Cell Towers to Connect
by Tom Simonite / September 29, 2014
A new feature being added to the LTE protocol that smartphones use to communicate with cellular towers will make it possible to bypass those towers altogether. Phones will be able to “talk” directly to other mobile devices and to beacons located in shops and other businesses. Known as LTE Direct, the wireless technology has a range of up to 500 meters, far more than either Wi-Fi or Bluetooth. It is included in update to the LTE standard slated for approval this year, and devices capable of LTE Direct could appear as soon as late 2015. LTE Direct has been pioneered by Qualcomm, which has been working on the technology for around seven years. At the mobile chip manufacturer’s Uplinq conference in San Francisco this month, it announced that it’s helping partners including Facebook and Yahoo experiment with the technology. Researchers are, for example, testing LTE Direct as a way to allow smartphones to automatically discover nearby people, businesses, and other information. Some see the technology as a potential new channel for targeted promotions or advertising.
Despite its long range, LTE Direct uses relatively little power, so a phone could be constantly looking for nearby devices without significantly draining its battery life. A device with LTE Direct active might discover other phones using the technology or communicate with beacons—fixed devices installed in businesses or integrated into the infrastructure of an airport or train station. “You can think of LTE Direct as a sixth sense that is always aware of the environment around you,” said Mahesh Makhijani, technical marketing director at Qualcomm, at a session on the technology. “The world around you is full of information, and the phone can use that to predict and to help you in your everyday life.”
Protests sprouted up in Kowloon shortly after demonstrations started on Hong Kong island. The protest site sits on the junction of two large highways and has blocked traffic.
Beacons using LTE Direct could broadcast useful information as well as special offers. A beacon installed in an airline check-in desk, for instance, might offer information on delays to people nearby who are booked on an affected flight. Facebook is exploring how the technology could be used with its mobile app. “LTE Direct would allow us to create user experiences around serendipitous interactions with a local business or a friend nearby,” said Jay Parikh, Facebook’s vice president of infrastructure engineering. “You could find out about events or do impromptu meet-ups.”

LTE Direct can be used much like the iBeacons announced by Apple last year, which retailers including Macy’s are testing as a way to track and connect with shoppers’ mobile devices. However, iBeacon devices use the Bluetooth protocol, which has a much shorter range, and which not everyone leaves switched on. Yahoo has also begun developing apps that use LTE Direct, says Beverly Harrison, a principal scientist at Yahoo Labs. One is a kind of digital tour guide. If you tell the app how long you have to spare, from 10 minutes to two hours, it will suggest a route past nearby points of interest, drawing on online information about places detected using LTE Direct. Harrison says Yahoo plans to start testing the app in January.
LTE Direct could also help smooth out the network glitches that occur when large numbers of users are trying to connect to the same cell tower. R/GA, an ad agency in New York whose clients include Nike and Beats, is designing a system that would use LTE Direct to serve up to a million people in or around Times Square on New Year’s Eve. Roman Kalantari, a creative director at RG/A, says LTE Direct is the only wireless technology that could keep devices online under such conditions. RG/A and a technology consultancy called Control Group are also interested in using LTE Direct to serve targeted promotions. A smartphone could use LTE Direct to signal to nearby businesses what types of foods or products a customer is interested in so that it can offer customized deals, says Kalantari. “The idea that every retailer could be observing purchase intent is extraordinary valuable,” he says.
In theory, LTE Direct could be used to create communication apps that route all data from device to device. Some chat apps can already use Wi-Fi and Bluetooth to link up nearby phones, but LTE Direct could offer extended range and better performance. However, carriers will control which devices on their networks can use LTE Direct because it uses the same radio spectrum as conventional cellular links. Wireless carriers might even gain a new stream of revenue by charging companies that want to offer services or apps using the technology, Qualcomm says.

Hong Kong protesters #handsupfriday
GOVERNMENT SPYWARE
http://www.theguardian.com/world/2014/sep/30/hong-kong-pro-democracy-protest-leaders-occupy
http://qz.com/274425/here-is-the-full-text-of-the-chinese-communist-partys-message-to-hong-kong/
http://blogs.wsj.com/chinarealtime/2014/09/25/pro-beijing-media-accuses-hong-kong-student-leader-of-u-s-government-ties/
https://www.lacoon.com/lacoon-discovers-xsser-mrat-first-advanced-ios-trojan/
http://www.theverge.com/2014/10/1/6877377/sophisticated-iphone-and-android-malware-is-spying-on-hong-kong
Sophisticated iPhone and Android malware is spying on Hong Kong protesters
by Amar Toor / October 1, 2014

Activists in Hong Kong practice being sprayed by water cannons during a September 7, 2014, drill in preparation for upcoming civil disobedience events. (Reuters/Tyrone Siu)
A fake smartphone app is being used to remotely monitor pro-democracy protesters in Hong Kong, according to a report from the New York Times. Researchers from Lacoon Mobile Security say the phishing scam is spreading across the messaging application WhatsApp, through texts that read: “Check out this Android app designed by Code4HK for the coordination of OCCUPY CENTRAL!”, along with a link to download software. Lacoon says the software, once downloaded, can access a user’s personal data, including phone calls, text messages, and the physical location of their smartphone. Code4HK — a developer community that has helped to spread information about the protests — tells the Times it had nothing to do with the texts.

“The CIA is everywhere, including in Hong Kong. Search the net for ‘Jimmy Lai and CIA’, and one will find a series of reports of how the CIA is using Jimmy Lai (owner of an unprofitable Apple Magazine) to channel tens of millions of dollars to opposition and democratic parties in Hong Kong. Lai is now under the investigation of ICAC (HK anti-corruption agency). A number of opposition parties in Hong Kong have confessed that they accepted money from Lai and did not declare it. This is a big news in Hong Kong.”
The origin of the scam remains unknown, but Lacoon CEO Michael Shaulov says the Chinese government is likely behind it, given the location of the servers and the sophistication of the operation. The company traced it to a computer that they say is similar to those that the Chinese government allegedly used to launch cyberattacks against US targets last year.
The spread of the app remains equally unclear, though Shaulov says it was downloaded by one out of every ten phones that received the fake message. It has affected both Android and iOS users alike, although many in the security world have noted that only jailbroken iOS phones are vulnerable. “This is the first time that we have seen such operationally sophisticated iOS malware operational, which is actually developed by a Chinese-speaking entity,” Shaulov told the Times. Similar iOS malware has been distributed by FinFisher, but never before linked to China.

Today’s report comes as thousands of protesters flocked to the streets on China’s National Day, calling for Beijing to allow for free democratic elections in 2017. China had previously said it would allow Hong Kong to choose its own leader by that date, but backtracked on that promise in August, when it announced that all candidates would have to be approved by Beijing. Protesters in the “Occupy Central” movement have clashed with police since protests escalated over the weekend, and there are fears of further confrontation tonight, during National Day celebrations.
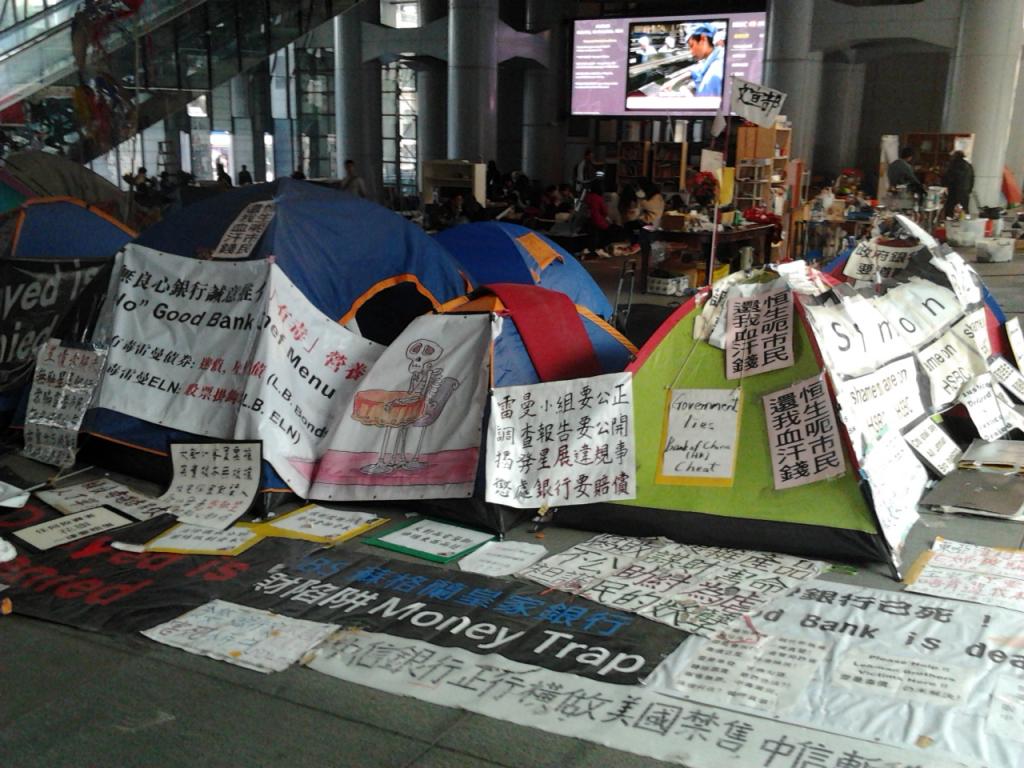
Hong Kong’s original Occupy movement
The Chinese government has gone to great lengths to censor news of the demonstrations. Most state-run media have not mentioned it, and Chinese web censors have stepped up efforts to block images and videos on social media. On Sunday, the government blocked access to Instagram within mainland China, and posts on the Twitter-like service Sina Weibo have been aggressively deleted, according to the Times. In the past few days, censors have blocked any Weibo posts including the words “Hong Kong,” “barricades,” and “umbrella” — the unofficial symbol of Hong Kong’s movement.

Oct 3: Taken away—Wang Zang 王藏, poet and vocal supporter of Occupy Central. At least seven mainlanders have been detained for their involvement in or support for the Occupy Central movement in Hong Kong, reports Human Rights In China. This does not include the Shenzhen activist who was taken away after posting photos of the Occupy Central movement on Weibo.
NETWORK BLACKOUTS
http://www.hrichina.org/en/detentions-mainland-related-occupy-central-movement-2014
http://shanghaiist.com/2014/09/29/instagram-blocked-mainland-china.php
http://advocacy.globalvoicesonline.org/2014/10/02/hong-kong-protesters-shore-up-mobile-communications-tools-in-face-of-technical-threats/
Hong Kong Protesters Shore Up Mobile Communications Tools in Face of Technical Threats
by inmediahk.net / 2 October 2014
This post was adapted in two segments from an article written by Oiwan Lam and originally published in Chinese on 1 October 2014 on citizen media platform inmediahk.net. It was translated by Loki Chu.
On September 28, after Hong Kong police unleashed tear gas on protesters, many said that they could not access the Internet with their mobile phones and had to run to Central or Wanchai districts before they could send their messages. Since then, a large number of protesters have downloaded FireChat to prepare for communication during network outages or network congestion. The FireChat application can run over a mesh network. As each mobile phone sends out a weak signal, a mesh network turns each mobile phone into a network node and links the nodes together to form a local telecommunication network that enables the exchange of messages between users. But Internet privacy and security experts warn that this software has security vulnerabilities and its users may become the targets of attacks. Calls may be intercepted and the locations of users may be tracked. The application also lacks a strong authentication system for users’ identities — it is relatively easy to impersonate another user, making the network vulnerable to infiltration by malicious actors.
| Applications | Anti-Monitor | Connectivity | System Compatibility |
| Serval Mesh | + For communication content and metadata (location, contacts, etc.) to encrypt | + Phone signal and Internet cut off time, but also be able to use | – No iOS version |
| FireChat | – Easy to be monitored: communication content and metadata can easily be accessed and monitored | + Phone signal and Internet cut off time, but also be able to use | + Android andiOS can be used on the system |
| ChatSecure | + Encrypts the communication content and metadata | – Can only be used when there is Internet | + Android andiOS can be used on the system |
| Redphone(Android) /Signal (iOs) | + Encrypts the communication content and metadata | – Can only be used when there is mobile phone signal |
Internet Society Hong Kong will organize a week with FireChat inventor Micha Benoliel the conference. The meeting will be webcast. Internet Society Hong Kong Facebook and Twitter. Chart found at https://pao-pao.net/article/194
Are there any tools that are more secure than FireChat and can be used during major network congestion? President of the Hong Kong Professional Information Security Association Eric Fan bluntly answered, “No.” He urged users not to download applications casually and not to jailbreak their iPhones or iPads because these actions are likely to pose security problems. Indeed, security vulnerabilities abound in this arena, and threats from mainland China are many. In mid-September, hackers distributed an Android application that was discovered to be spyware capable of stealing information from users’ smartphones and tracking users’ locations on Baidu Maps, a mainland Chinese version of Google Maps. The hackers disguised themselves as Code4HK, a group of tech geeks who support social movements in Hong Kong. Fan pointed out that, in fact, many applications have security vulnerabilities, and users must be vigilant in protecting their communication tools. In addition, under a good network connection, he recommends the use of Telegram. Telegram is an application similar to WhatsApp, but all communications are encrypted and users may choose to delete conversation records permanently to prevent old records from being spied upon if a user’s mobile phone or computer is confiscated. This particular point is important for activists who are targets of political persecution. It is now common practice for Hong Kong police to confiscate protest organizers’ mobile phones, and in some cases, they even obtain search warrants and confiscate personal computers for investigation. Google Talk is another common communication tools among protesters. It is prudent to develop the habit of choosing the “off-the-record” chat option so that others cannot read the chat history.
iOS SPYWARE
http://www.inmediahk.net/node/1026710
http://mobile.reuters.com/article/idUSL2N0RV2D320140930?irpc=932
Advanced iOS virus targeting Hong Kong protestors -security firm
reporting by Jim Finkle; edit by Richard Valdmanis / Sep 30, 2014
Cybersecurity researchers have uncovered a computer virus that spies on Apple Inc’s iOS operating system for the iPhone and iPad, and they believe it is targeting pro-democracy protesters in Hong Kong. The malicious software, known as Xsser, is capable of stealing text messages, photos, call logs, passwords and other data from Apple mobile devices, researchers with Lacoon Mobile Security said on Tuesday. They uncovered the spyware while investigating similar malware for Google Inc’s Android operating system last week that also targeted Hong Kong protesters. Anonymous attackers spread the Android spyware via WhatsApp, sending malicious links to download the program, according to Lacoon. It is unclear how iOS devices get infected with Xsser, which is not disguised as an app. Lacoon Chief Executive Michael Shaulov told Reuters that Xsser is the most sophisticated malware used to date in any known cyberattack on iOS users. “This is one the most interesting developments we have seen,” he said. “It’s the first real indication that really sophisticated guys are shifting from infecting PCs or laptops to going after iOS devices.”
The code used to control that server is written in Chinese. The high quality of the campaign and the fact it is being used to target protesters suggests that it is coming from a sophisticated attacker in China, Shaulov said. “It is the first time in history that you actually see an operationalized iOS Trojan that is attributed to some kind of Chinese entity,” he said. A Trojan is a term used by cyber researchers to describe malware that enters a device disguised as something harmless. Still, he said that his company’s research team has yet to identify any specific victims of the iOS Trojan. Lacoon said on its blog that it is possible the attackers might have deployed the Trojan in other places, in addition to spying on pro-democracy protesters in Hong Kong. “It can cross borders easily, and is possibly being operated by a Chinese-speaking entity to spy on individuals, foreign companies, or even entire governments,” they said in a blog post describing their analysis.
KILL SWITCHES
http://globalvoicesonline.org/2014/10/02/fears-of-a-network-blackout-still-loom-for-hong-kongs-pro-democracy-protesters/
by inmediahk.net / 2 October 2014
On September 28, rumors that Hong Kong police had asked mobile phone operators to shut down network services in Hong Kong’s Admiralty area spread like wildfire. Tensions were already running high, as police had used tear gas on pro-democracy protesters just hours before. The Federation of University Student Unions, a key organization that has helped mobilize the massive sit-in dubbed Occupy Central, immediately called for protesters to retreat from the demonstration if network services were cut. On social media, messages from various sources urging protesters to download and install FireChat, a chat application that can be used over the Internet or via Bluetooth technology, went viral. The FireChat Bluetooth setting allows users within close proximity to one another to communicate without a mobile Internet connection. Scores of protesters downloaded FireChat in an effort to maintain communication during the protest in case of a network shutdown, despite the inherent security vulnerabilities that the app carries. Thus far however, a network shutdown has not taken place.
Many are now wondering if it is even possible for a network blackout to be imposed on Hong Kong. This happens on a regular basis in regions of mainland China like Xinjiang, where authorities use Internet blackouts to contain ethnic unrest among the region’s Uyghur minority. Yet network infrastructure and corporate governance is much less tightly controlled in the special administrative region of Hong Kong. Charles Mok, the legislative councillor for the Information Technology Functional Constituency, believes that the chance of a network blackout is very slim.
Two ordinances regulate the government’s power to impose a network blackout. Hong Kong’s Telecommunications Ordinance says in the face of a public emergency, if the chief executive (highest authority in the region) decides that the government must exert control over telecommunication stations, he can sign a warrant to do so and use the networks instead for public messages. Although the warrant cannot remain in effect for more than one week, successive warrants from week to week may be issued. This ordinance, however, does not define “emergency.” The region’s Emergency Regulations Ordinance states that “on any occasion in which the chief executive in Council may consider to be an occasion of emergency or public danger, he may make any regulations whatsoever that he may consider desirable in the public interest.” In other words, Hong Kong needs to be in a state of (a vaguely-defined) “emergency” for the government to demand Internet providers to shut down their networks, whether throughout the whole territory or in a specific region.
Charles Mok pointed out that the government would have difficulty exercising the power given by these two ordinances because both mobile network services and fixed line network services operate in open markets in Hong Kong. According to data provided by the Hong Kong Trade Development Council, there are a total of 20 local fixed line telecommunications network operators as of June 2013, five mobile network operators as of December 2012 and 194 Internet service providers as of June 2013. One can imagine the huge impact should a Cap 106 warrant be issued. Moreover, the warrant must be sent directly to either the CEO or CTO of the service providers, and before overseas operators receive these warrants, the network should remain connected. Charles Mok added that should the government really want to disconnect the network, it may still be done with the 3G and 4G mobile network operators, but once the network is cut, mobile phone voice services will also be terminated, and the impact will be impossible to measure.
#Hong Kong: Twitter Reverb is a Twitter-owned tool that illustrates how conversation unfolds on the social network. The blue line tracks tweet per minute
CHOKE POINTS
http://advocacy.globalvoicesonline.org/2013/12/17/in-chinas-ethnic-minority-regions-internet-blackouts-are-the-norm/
In Tibet and Uyghur Regions, Internet Blackouts Are the Norm
by Oiwan Lam / 17 December 2013
… as we approached Aba County, something changed. I stopped getting messages on WeChat and QQ, China’s most popular mobile apps…When I tried to load e-mail, an error occurred: “Could not authenticate cellular data network: PDP authentication failure.” I still had a signal—the little 3G icon was there and everything. But the signal didn’t seem to contain any data.
Stories of Internet censorship in China often focus on surveillance and social media filtering, practices that violate the rights to free expression and privacy of all users in mainland China. But those living in remote, embattled ethnic minority regions of the country face a far more bleak reality when it comes to using the Internet.
Prolonged network shutdowns have become a regular occurrence in Uyghur and Tibetan minority regions of western China, as Christopher Beam describes in the New Republic article quoted above. Chinese authorities believe that foreign forces, such as the Tibetan Government in Exile and World Uyghur Congress are involved in the organization of separatist activities in China. Seeking to contain unrest and discontent in conflict areas, authorities have imposed Internet shutdowns, depriving individuals of their right to communication online. In some extreme cases, network shutdowns have extended to local mobile networks.
This kind of “political punishment” began in Tibetan Autonomous Prefectures with 2008 political riots in Lhasa. The Internet was shutdown in March of 2008, and briefly restored in December 2008, only to be cut off again a few months later when the first self-immolation protest took place. Internet access has remained unstable in the area ever since.
According to Tibetan dissident writer Woeser’s blog, Internet and mobile SMS connections for more than 18 counties from Garze Tibetan Autonomous Prefecture were cut off from the global Internet for at least three months beginning in February 2009. A number of counties in Aba Prefecture, predominantly Tibetan, suffered a similar fate. Connection disruptions now have become a norm in conflict areas where self-immolation protests and anti-government demonstrations are frequent. Most recently, a network shutdown occurred in Diru county, following protests against a policy that required Tibetans in a local village to put Chinese national flags on their rooftops. The Xinjiang region, mainly populated by the Muslim Uyghur minority group, has faced similar challenges. Amid protests in 2009, residents faced a nearly year-long Internet shutdown and were even deprived of telephone service for a week at the height of the unrest. Since then, network disruptions have happened on a smaller scale during politically sensitive periods. In March 2013, protests erupted after a seven-year-old Uyghur boy was stabbed to death by a Han Chinese in Piqan county of Turpan Prefecture, leading to a three-day Internet blackout. This past June, the Internet was again shut down temporarily in Urumqi to stop the spread of rumors related to forced demolitions in Piqan county — 27 people were killed [zh] in riots during a violent confrontation between protestors and police surrounding the demolitions.
Hong Kong's tech-savvy protesters are going digitally dark as they try to avoid surveillance and potential future prosecutions, disabling location tracking on their phones, buying train tickets with cash and purging their social media conversations. By me https://t.co/D7d843rTgh
— Elaine Yu (@yuenok) June 13, 2019
These shutdowns have violated citizens’ rights to communication of expression, and have left them unable to seek information, goods, and services through the Internet. They have also given local authorities a monopoly on information — control over news and analysis of these regional conflicts now sits firmly in the hands of the government. For example, the above-mentioned demolition protest in Piqan county was characterized as a “terrorist attack” by state media. When the Uyghur community attempted to report on the situation, spreading an alternative version of the story using Sina Weibo, the Internet blackout expanded from Piqan county to Urumqi, the largest city in Xinjiang. Citizen journalists in Bachu county faced a similar situation last month, when both local authorities and state media quickly labeled riots as a terrorist attack, thus justifying an information crackdown. Many Han Chinese have fully embraced official state explanations of conflicts in Xinjiang and have even criticized ethnic groups for not being grateful for preferential ethnic policies, such as exemption from the One-Child Policy. As the online public sphere has been dominated by Han Chinese, mainstream public opinion has further marginalized ethnic communities in unrest areas.
New use for Hong Kong’s protest umbrellas — blocking surveillance cameras round police headquarters. Everyone cheered when this one finally went up pic.twitter.com/FuZYbspKsj
— Emma Graham-Harrison (@_EmmaGH) June 21, 2019
Internet shutdowns in China have not been limited to areas of ethnic conflict. In June 2009, the Internet was shut down for a few days in the Hubei province city of Shishou, following riots triggered by the alleged murder of a young woman working in a local hotel. But Shishou is connected with other cities by a major highway — information about the incident and crackdown spread through Chinese social media and was even translated into English for global readers. Ultimately, the shutdown did not paralyze the city as it might have in Xinjiang or Tibet. Within the Chinese Communist Party, many have questioned the value of this “hard” practice of social control. Softer approaches have been used in much of the country and seen as effective, but they have not been applied to far west border areas where conflict has become endemic. With state officials suggesting that ethnic minorities may be linked to terrorist organizations, they have justified harder tactics on the grounds that these groups are a risk to national security.
“Recycle” — Hong Kong’s wonderfully civic-minded protestors, at one of their self-organised clean-up spots pic.twitter.com/AMPmcXjlM2
— Emma Graham-Harrison (@_EmmaGH) June 17, 2019
Thus far, Internet shutdowns in China have been regional and targeted at specific areas of unrest, with one exception — for an hour in April 2012, all users in mainland China were unable to visit overseas websites and foreign IPs could not access the Chinese network. Many speculated that the disruption was caused by the upgrade of the Chinese Great Firewall. The incident demonstrated the ability of the Chinese authority to cut off the domestic network if and when necessary.
Occupiers are doing one last sweep for rubbish. 2 million people marched here yesterday, it was occupied all night, and there isn’t a scrap of rubbish on the road. #HK people…! pic.twitter.com/JE8D4f4iCL
— Brian Kern / Kong Tsung-gan / 江松澗 (@KongTsungGan) June 17, 2019
More and more countries have begun to resort to Internet shutdowns when facing mass protests. During the Arab Spring, both the Mubarak regime in Egypt and the Assad regime in Syria severed Internet connections in an effort to control protests. A nation-wide Internet blackout took place in Sudan after riots erupted in northern Khartoum in September 2013. But while shutdowns have lasted just a few days in most of these cases, China’s minority regions face a different paradigm. Prolonged blackouts have exacerbated minority citizens’ marginalization. Literally disconnected from the rest of the country, these communities have been left on the wrong side of what appears to be a growing digital divide.
PREVIOUSLY
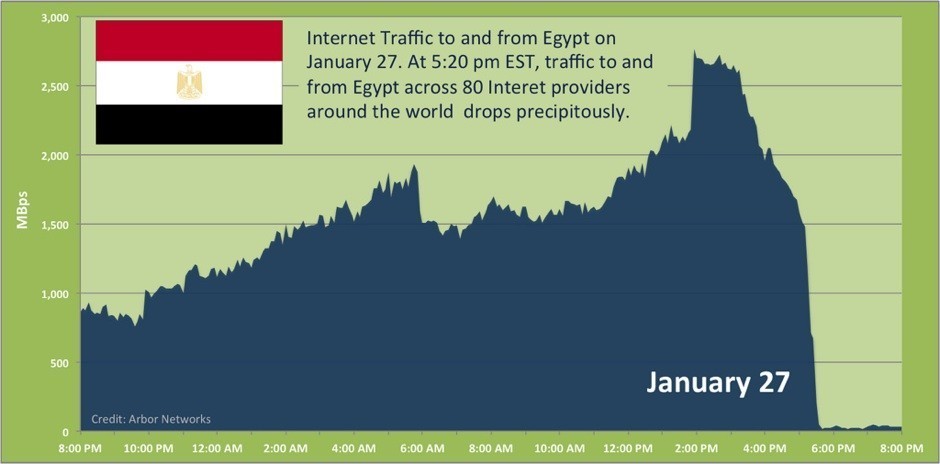
EGYPT SHUTS DOWN INTERNET : U.S. PROPOSES INTERNET KILL SWITCH
http://spectrevision.net/2011/01/28/egypt-shuts-down-internet/
http://spectrevision.net/2011/02/11/mesh-phone-networks/
IRANIAN ELECTION FAKED OUTRIGHT : IRAN’S PROXY FIGHT
http://spectrevision.net/2009/06/19/what-tipped-you-off/