http://wikileaks.ch/Evidence-of-torture-and-repression.html
http://wikileaks.ch/cable/2007/05/07CAIRO1417.html
http://wikileaks.ch/cable/2009/07/09CAIRO1447.html
http://www.telegraph.co.uk/news/worldnews/africaandindianocean/egypt/8288163/How-Egypt-shut-down-the-internet.html
How Egypt shut down the internet
by Christopher Williams / 28 Jan 2011
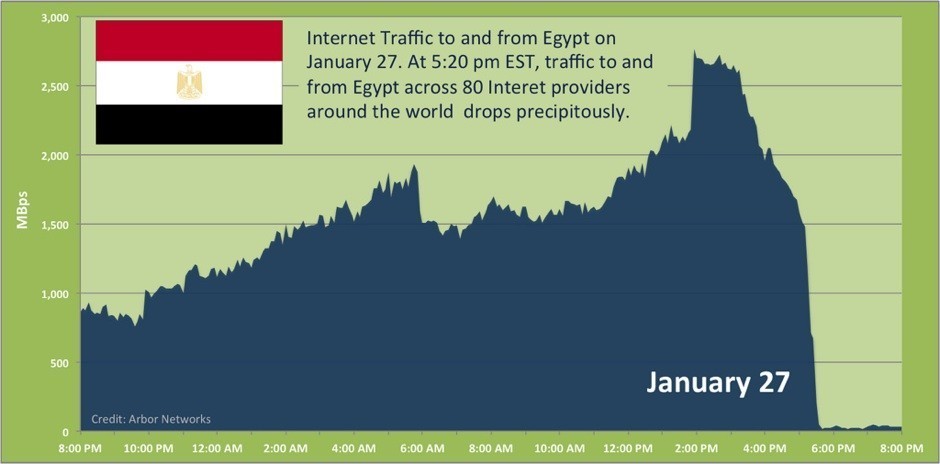
Organisations that track global internet access detected a collapse in traffic in to and out of Egypt at around 10.30GMT on Thursday night. The shut down involved the withdrawal of more than 3,500 Border Gateway Protocol (BGP) routes by Egyptian ISPs, according to Renesys, a networking firm. Only one ISP out of 10, Noor Data Networks, appeared largely unaffected. It connects to the outside world via an undersea cable operated by Telecom Italia. According to BGPMon, another networking firm, 88 per cent of Egyptian internet access was successfully shut down, however. Renesys speculated that the apparent anomaly of Noor Data Networks may be a result of the fact it provides services to the Egyptian stock exchange. BGP routes are one of the most vital parts of the internet. They are mostly used by ISPs so their networks can exchange information about how to best route the packets of data that make up all internet communications.
If an ISP withdraws its BGP routes, its customers effectively disappear from the internet, unable to access websites and services, send and receive email, or use voice services such as Skype. The Egyptian government’s action is unprecedented in the history of the internet. Countries such as China, Iran, Thailand and Tunisia have cut off access to news websites and social networking services during periods of unrest, as Egypt did when it cut off Facebook and Twitter earlier this week. The ongoing attempt by the Egyptian government to shut down all online communication is, however, a new phenomenon. It not only prevents ordinary Egyptian internet users from accessing any websites, it cripples Tor, an anti-censorship tool that technical experts and activists were using to circumvent the Facebook and Twitter blocks. The action puts Egypt, temporarily at least, in the company of North Korea, which has never allowed its citizens access to the internet.

http://www.noor.net/network.aspx
http://www.renesys.com/blog/2011/01/egypt-leaves-the-internet.shtml
Egypt Leaves the Internet
by James Cowie / January 27, 2011
Confirming what a few have reported this evening: in an action unprecedented in Internet history, the Egyptian government appears to have ordered service providers to shut down all international connections to the Internet. Critical European-Asian fiber-optic routes through Egypt appear to be unaffected for now. But every Egyptian provider, every business, bank, Internet cafe, website, school, embassy, and government office that relied on the big four Egyptian ISPs for their Internet connectivity is now cut off from the rest of the world. Link Egypt, Vodafone/Raya, Telecom Egypt, Etisalat Misr, and all their customers and partners are, for the moment, off the air. At 22:34 UTC (00:34am local time), Renesys observed the virtually simultaneous withdrawal of all routes to Egyptian networks in the Internet’s global routing table. Approximately 3,500 individual BGP routes were withdrawn, leaving no valid paths by which the rest of the world could continue to exchange Internet traffic with Egypt’s service providers. Virtually all of Egypt’s Internet addresses are now unreachable, worldwide.
This is a completely different situation from the modest Internet manipulation that took place in Tunisia, where specific routes were blocked, or Iran, where the Internet stayed up in a rate-limited form designed to make Internet connectivity painfully slow. The Egyptian government’s actions tonight have essentially wiped their country from the global map. What happens when you disconnect a modern economy and 80,000,000 people from the Internet? What will happen tomorrow, on the streets and in the credit markets? This has never happened before, and the unknowns are piling up. We will continue to dig into the event, and will update this story as we learn more. As Friday dawns in Cairo under this unprecedented communications blackout, keep the Egyptian people in your thoughts.
Update (3:06 UTC)
One of the very few exceptions to this block has been Noor Group (AS20928), which still has 83 out of 83 live routes to its Egyptian customers, with inbound transit from Telecom Italia as usual. Why was Noor Group apparently unaffected by the countrywide takedown order? Unknown at this point, but we observe that the Egyptian Stock Exchange (www.egyptse.com) is still alive at a Noor address. Its DNS A records indicate that it’s normally reachable at 4 different IP addresses, only one of which belongs to Noor. Internet transit path diversity is a sign of good planning by the Stock Exchange IT staff, and it appears to have paid off in this case. Did the Egyptian government leave Noor standing so that the markets could open next week?

http://www.readwriteweb.com/hack/2011/01/egypt-tor-use-skyrocketing-as.php
Tor Use Skyrocketing as Users Route-Around Internet Blocks
by Klint Finley / January 28, 2011
As we reported yesterday, the Egyptian government appears to be locking down Intrernet access in Egypt. Access in or out of the country seems to be blocked. GigaOm provides some analysis on how this might work. However, some Egyptian Internet users are still able to access the outside Internet. The Washington Post lists some ways that Egyptians are still accessing the Internet. Meanwhile, use of Tor, a free Internet anonymizer, is skyrocketing.
According to the Post:
- Noor Data Networks, the provider used by the Egyptian Stock Excahnge, is unaffected by the Internet blackout.
- Some are using dial-up access routed through other countries, though there are reports that some landlines are down.
- Some are using virtual private networks.
It’s being widely retweeted that a French ISP called French Data Network is offering free dial-up to Egyptians: “Free dialup internet access for egypt : http://www.fdn.fr on +33172890150 login toto password toto #jan25 #egypt MASS RT PLZ”
Many people on Twitter are calling for people in other countries to setup Tor relays.
It’s probably worth revisiting the failure of Haystack, an interesting but badly flawed attempt at anonymizing Internet traffic. Perhaps this will also rekindle interest in projects like Freenet and Netsukuku.
DIY AD-HOC WIFI
http://www.pcworld.com/article/218155/get_internet_access_when_your_government_shuts_it_down.html
Get Internet Access When Your Government Shuts It Down
by Patrick Miller & David Daw / Jan 28, 2011
These days, no popular movement goes without an Internet presence of some kind, whether it’s organizing on Facebook or spreading the word through Twitter. And as we’ve seen in Egypt, that means that your Internet connection can be the first to go. Whether you’re trying to check in with your family, contact your friends, or simply spread the word, here are a few ways to build some basic network connectivity when you can’t rely on your cellular or landline Internet connections.
Do-It-Yourself Internet With Ad-Hoc Wi-Fi
Even if you’ve managed to find an Internet connection for yourself, it won’t be that helpful in reaching out to your fellow locals if they can’t get online to find you. If you’re trying to coordinate a group of people in your area and can’t rely on an Internet connection, cell phones, or SMS, your best bet could be a wireless mesh network of sorts–essentially, a distributed network of wireless networking devices that can all find each other and communicate with each other. Even if none of those devices have a working Internet connection, they can still find each other, which, if your network covers the city you’re in, might be all you need. At the moment, wireless mesh networking isn’t really anywhere close to market-ready, though we have seen an implementation of the 802.11s draft standard, which extends the 802.11 Wi-Fi standard to include wireless mesh networking, in the One Laptop Per Child (OLPC) XO laptop. However, a prepared guerrilla networker with a handful of PCs could make good use of Daihinia ($25, 30-day free trial), an app that piggybacks on your Wi-Fi adapter driver to turn your normal ad-hoc Wi-Fi network into a multihop ad-hoc network (disclaimer: we haven’t tried this ourselves yet), meaning that instead of requiring each device on the network to be within range of the original access point, you simply need to be within range of a device on the network that has Daihinia installed, effectively allowing you to add a wireless mesh layer to your ad-hoc network. Advanced freedom fighters can set up a portal Web page on their network that explains the way the setup works, with Daihinia instructions and a local download link so they can spread the network even further. Lastly, just add a Bonjour-compatible chat client like Pidgin or iChat, and you’ll be able to talk to your neighbors across the city without needing an Internet connection.
Back to Basics
Remember when you stashed your old modems in the closet because you thought you might need them some day? In the event of a total communications blackout–as we’re seeing in Egypt, for example–you’ll be glad you did. Older and simpler tools, like dial-up Internet or even ham radio, could still work, since these “abandoned” tech avenues aren’t being policed nearly as hard. In order to get around the total shutdown of all of the ISPs within Egypt, several international ISPs are offering dial-up access to the Internet to get protesters online, since phone service is still operational. It’s slow, but it still works–the hard part is getting the access numbers without an Internet connection to find them. Unfortunately, such dial-up numbers can also be fairly easily shut down by the Egyptian government, so you could also try returning to FidoNet–a distributed networking system for BBSes that was popular in the 1980s. FidoNet is limited to sending only simple text messages, and it’s slow, but it has two virtues: Users connect asynchronously, so the network traffic is harder to track, and any user can act as the server, which means that even if the government shuts down one number in the network, another one can quickly pop up to take its place. You could also take inspiration from groups that are working to create an ad-hoc communications network into and out of Egypt using Ham Radio, since the signals are rarely tracked and extremely hard to shut down or block. Most of these efforts are still getting off the ground, but hackers are already cobbling together ways to make it a viable form of communication into and out of the country.
Always Be Prepared
In the land of no Internet connection, the man with dial-up is king. Here are a few gadgets that you could use to prepare for the day they cut the lines. Given enough time and preparation, your ham radio networks could even be adapted into your own ad-hoc network using Packet Radio, a radio communications protocol that you can use to create simple long-distance wireless networks to transfer text and other messages between computers. Packet Radio is rather slow and not particularly popular (don’t try to stream any videos with this, now), but it’s exactly the kind of networking device that would fly under the radar. In response to the crisis in Egypt, nerds everywhere have risen to call for new and exciting tools for use in the next government-mandated shutdown. Bre Pettis, founder of the hackerspace NYC Resistor and creator of the Makerbot 3D printer, has called for “Apps for the Appocalypse,” including a quick and easy way to set up chats on a local network so you can talk with your friends and neighbors in an emergency even without access to the Internet. If his comments are any indication, Appocalypse apps may be headed your way soon. Tons of cool tech are also just waiting to be retrofitted for these purposes. David Dart’s Pirate Box is a one-step local network in a box originally conceived for file sharing and local P2P purposes, but it wouldn’t take much work to adapt the Pirate Box as a local networking tool able to communicate with other pirate boxes to form a compact, mobile set of local networks in the event of an Internet shutdown.

INFORMATION MANAGEMENT
http://gigaom.com/2011/01/28/how-egypt-switched-off-the-internet/
How Egypt Switched Off the Internet
by Bobbie Johnson / Jan 28, 2011
Amid spreading protests, the Egyptian government has taken the incredible step of shutting down all communications late Thursday. Only a handful of web connections, including those to the nation’s stock exchange, remain up and running. It’s an astonishing move, and one that seems almost unimaginable for a nation that not only has a relatively strong Internet economy but also relies on its connections to the rest of the world. But how did the government actually do it? Is there a big kill switch inside Egyptian President Hosni Mubarak’s office? Do physical cables have to be destroyed? Can a lockdown like this work?
Plenty of nations place limitations on communications, sometimes very severe ones. But there are only a few examples of regimes shutting down communications entirely — Burma’s military leaders notably cut connectivity during the protests of 2007, and Nepal did a similar thing after the king took control of the government in 2005 as part of his battle against insurgents. Local Chinese authorities have also conducted similar, short-lived blockades. The OpenNet Initiative has outlined two methods by which most nations could enact such shutdowns. Essentially, officials can either close down the routers which direct traffic over the border — hermetically sealing the country from outsiders — or go further down the chain and switch off routers at individual ISPs to prevent access for most users inside.
In its report on the Burmese crackdown, ONI suggests the junta used the second option, something made easier because it owns the only two Internet service providers in the country.
The Burmese Autonomous System (AS), which, like any other AS, is composed of several hierarchies of routers and provides the Internet infrastructure in-country. A switch off could therefore be conducted at the top by shutting off the border router(s), or a bottom up approach could be followed by first shutting down routers located a few hops deeper inside the AS.
A high-level traffic analysis of the logs of NTP (Network Time Protocol) servers indicates that the border routers corresponding to the two ISPs were not turned off suddenly. Rather, our analysis indicates that this was a gradual process.
While things aren’t clear yet, this doesn’t look like the pattern seen in Egypt, where the first indications of Internet censorship came earlier this week with the blockades against Twitter and Facebook, but when access disappeared, it disappeared fast, with 90 percent of connections dropping in an instant.
Analysis by Renesys, an Internet monitoring body, indicates the shutdown across the nation’s major Internet service providers was at precisely the same time, 12:34 a.m. EET (22:34 UTC):
Renesys observed the virtually simultaneous withdrawal of all routes to Egyptian networks in the Internet’s global routing table … The Egyptian government’s actions tonight have essentially wiped their country from the global map.
Instead, the signs are that the Egyptian authorities have taken a very careful and well-planned method to screen off Internet addresses at every level, from users inside the country trying to get out and from the rest of the world trying to get in.
“It looks like they’re taking action at two levels,” Rik Ferguson of Trend Micro told me. “First at the DNS level, so any attempt to resolve any address in .eg will fail — but also, in case you’re trying to get directly to an address, they are also using the Border Gateway Protocol, the system through which ISPs advertise their Internet protocol addresses to the network. Many ISPs have basically stopped advertising any internet addresses at all.”
Essentially, we’re talking about a system that no longer knows where anything is. Outsiders can’t find Egyptian websites, and insiders can’t find anything at all. It’s as if the postal system suddenly erased every address inside America — and forgot that it was even called America in the first place. A complete border shutdown might have been easier, but Egypt has made sure that there should be no downstream impact, no loss of traffic in countries further down the cables. That will ease the diplomatic and economic pressure from other nations, and make it harder for protesters inside the country to get information in and out.
Ferguson suggests that, if nothing else, the methods used by the Egyptian government prove how fragile digital communication really is. “What struck me most is that we’ve been extolling the virtues of the Internet for democracy and free speech, but an incident like this demonstrates how easy it is — particularly in a country where there’s a high level of governmental control — to just switch this access off.”
MADE IN USA
http://edition.cnn.com/2011/WORLD/africa/01/28/egypt.us.tear.gas/
Controversial tear gas canisters made in the USA
by Emily Smith / January 28, 2011
A thick pall of chemical smoke hung over a crowd in Cairo on Friday afternoon. People ran, covering their noses and mouths to escape yet another volley of tear gas. The same scene was being played out elsewhere in Cairo, in Alexandria and Suez. And several weeks back, Tunisian police used tear gas to try to quell protests there. It is one of the most common ways to used to disperse protests — but not everyone runs.
In both Tunisia and Egypt, some protesters stopped to pick up canisters, and posted photographs online. A few inches long, blue and silver, they include warning labels and then a set of initials: CSI, followed by “Made in the U.S.A.” The photograph posted in Tunisia was of a 40 mm riot CS smoke projectile, made by a company called Combined Systems Inc., which describes itself as a “tactical weapons company” and is based in Jamestown, Pennsylvania. CSI’s website describes the projectile as “a launched burning extended-range single projectile round that dispenses smoke or chemical agents via rapid burning. Used effectively during riots at safe stand-off distances to disperse groups or deny areas.” Its warning label reads: “Danger: Do not fire directly at person(s). Severe injury or death may result.”
That warning is apparently not always followed. Lucas Mebrouk Dolega died in Tunisia on January 17, three days after being hit by a tear gas grenade at close range. The 32-year-old was a photographer for the European PressPhoto Agency. On Thursday, a similar picture was posted on Twitter by a someone in Egypt, only this time it was of a grenade, not a canister. It, too, was made by CSI. The grenade appears to be an “Outdoor 52 Series Large Grenade” that “discharges a high volume of smoke and chemical agent through multiple emission ports. Specifically for outdoor use,” the website says.
CSI’s website (www.less-lethal.com) bills the company as the “premier engineering, manufacturing and supply company of tactical munitions and crowd control devices globally to armed forces, law enforcement, corrections and homeland security agencies.” Clients include the U.S. Army, U.S. Customs and Border Patrol, and the U.S. Department of State, as well as Rafael Advanced Defense Systems and Israeli Military Industries — both of which are weapons companies based in Israel. On January 1, Jawaher Abu Rahmah died in the West Bank during a weekly protest against a security barrier being built in Bilin. Israel considers the protests violent and illegal. Rahmah died of severe asphyxiation and cardiac arrest after Israeli soldiers fired tear gas canisters into the crowd. In April 2009, Rahmah’s brother was killed participating in the same weekly protest when a tear gas canister struck him directly in the chest.
A spokesman for CSI says the company is operating well within the law by selling tear gas to countries like Tunisia and Egypt. According to the Chemical Weapons Convention, riot control agents are not considered chemical weapons unless used during a time of war. This means that it’s perfectly legal to manufacture and sell tear gas, so long as countries don’t stockpile a large amount of the chemical compounds. The spokesman declined to say how much tear gas CSI had sold to countries in northern Africa, but said it is a small company. He also said CSI could not control how its products are used once sold. Social media reaction to the “Made in the U.S.A.” label on the canisters was scathing, with some suggesting it meant the U.S. government itself was somehow involved in suppressing the protests. Some Twitter users demanded to know “why so many weapons used against Egyptian protesters read ‘made in the USA’.” Others advised “Maybe U.S. weapons manufacturers should stop printing “made in USA” on their weapons especially the ones we send to brutal autocrats.”
Whether CSI is operating within the law hasn’t stopped protestors from voicing their dissatisfaction with the company. After Rahmah died in Israel, demonstrators gathered outside Point Lookout Capital Partners’ Manhattan offices. Point Lookout owns a majority interest in CSI. The protesting group — the New York Campaign for the Boycott of Israel — demanded that CSI stop providing tear gas that could be used on Palestinians by Israeli forces. Israeli authorities are still investigating Jawaher Abu Rahmah’s death. According to the Centers for Disease Control and Prevention, there are several compounds that are considered to be riot-control agents. Two of the most common are chloroacetophenone (CN) and chlorobenzylidene malononitrile (CS). Others include chloropicrin (PS), bromobenzylcyanide (CA), and dibenzoxazepine (CR). Riot control agents temporarily disable those affected by causing irritation to the eyes, mouth, throat, lungs, and skin. Long-lasting exposure to these compounds can cause blindness and chemical burning of the throat and lungs resulting in death, as well as respiratory failure, which can also result in death.

U.S. CHAMBER of COMMERCE WEIGHS IN
http://www.npr.org/2011/01/28/133306560/world-markets-sink-as-protests-escalate-in-egypt
http://ftalphaville.ft.com/blog/2011/01/28/473431/us-foreign-aid-to-egypt/
http://thinkprogress.org/2011/01/27/us-chamber-egyptian-dictatorship/
How the U.S. Chamber of Commerce’s Egyptian Affiliate Went to Bat for the Egyptian Dictatorship
by Zaid Jilani / Jan 27th, 2011
As Egyptian protests continue to rage and thousands of people in that country continue to demand democratic reforms, manycommentators are rightly calling upon the international community to show solidarity with the demonstrators and join them in battling the Mubarak regime. However, there is at least one powerful, multinational entity that has continually stood by Mubarak and the Egyptian elite and has continually fought efforts to democratize the country. As ThinkProgress previously reported, the U.S. Chamber of Commerce maintains a network of foreign affiliates known as Amchams, “which are foreign chambers of the Chamber composed of American and foreign companies.” In Egypt, this foreign affiliate is known as the American Chamber of Commerce in Egypt, known in short as AmCham Egypt.
AmCham Egypt’s relation to the Mubarak dictatorship stretches back decades. In fact, the Egyptian dictator even personally intervened to create the organization. In 1981, Mubarak issued an order to allow for the creation of the AmCham by giving it an exemption from Egypt’s strict NGO laws — which help limit the influence human rights and democracy promotion organizations. Since then, the chamber has grown to have hundreds of members. While roughly 75 percent of the organization’s members are Egyptian businesses, many of them are also large Western multinational corporations, like Coca Cola and BP. The Chamber’s member companies account for nearly 20 percent of Egypt’s GDP.
When a powerful corporate-backed entity like the AmCham Egypt gains favorable treatment, it is natural for it to try to protect its patron. So last year, when a group of U.S. Senators — lead by Russ Feingold (D-WI) — introduced legislation that called on the government of Egypt to end crackdowns on pro-democracy activists and hold free and fair elections, AmCham Egypt, at the behest of the Egyptian dictatorship, sprung into action. As Al Masra Al Youm, a major Egyptian paper, reports, the Mubarak regime tapped AmCham Egypt President Shafik Gabr to do its bidding. Gabr was “dispatched expressly” for the purpose of scuttling the bill:
American Chamber of Commerce (AmCham) in Egypt President Shafik Gabr arrived in Washington on Wednesday to meet with members of US Congress in an effort to persuade them to refrain from issuing a resolution demanding that Egypt “hold fair elections, allow international monitoring of elections, and respect democracy and human rights.”
Informed sources told Al-Masry Al-Youm that Gabr, who is also a leading member of the ruling National Democratic Party of President Hosni Mubarak, had been dispatched expressly for this purpose by the Egyptian government.
By asking a non-American who technically worked for a nongovernmental organization to do their advocacy for them, the Mubarak regime successfully skirted numerous laws dealing with lobbying disclosure, making it easier to hide its role. But thanks to the intervention of AmCham Egypt as well as a multi-million dollar official lobbying campaign by Mubarak, the bill died a quiet death as it wasn’t brought to the floor before the Senate’s recess.

And stunningly, just days before massive protests erupted all over Egypt demanding democracy — protests which were widely expected given events in neighboring Tunisia and the upcoming anniversary of a police massacre at the hands of British colonizers — AmCham Egypt hosted former U.S. Deputy Secretary of State John Negroponte, who blamed the media for its “sensational coverage” of the Tunisian revolution and said it was in American interests to “continue to support ‘our friends’ in the region, such as Egypt, Jordan and Gulf countries.” “Chaos is in no one’s interest,” he concluded, disparaging the protests:
Negroponte said it will be crucial for US interests to continue to support “our friends” in the region, such as Egypt, Jordan and Gulf countries. […] During a brief question-and-answer session at the conclusion of his address, Negroponte said he was surprised by the unrest in Tunisia that ended the 23-year presidency of Zine El Abidine Ben Ali. He said that what happened in Tunisia is “not necessarily transferable” to other countries. He blamed the news media for sensational coverage of self-immolation protests in Egypt, Algeria and Mauritania, and urged “a little bit of patience.” “Let’s hope the country doesn’t descend into chaos,” he said. “Chaos is in no one’s interest.”
While backing dictatorships is nothing new for Negroponte, it should be noted that he has financial interests at stake in Egypt as well. He is on the board of Agility DGS, a defense company that has major operations in Egypt.
In 2006, AmCham Egypt, in a particularly outlandish move, put out a statement in its Business Monthly that bragged that President Mubarak “became Egypt’s first president to be directly elected in a multiparty contest” in 2005 — a reference to an election where almost all the independent opposition was banned and Mubarak won 88 percent of the vote. For years, the U.S. Chamber of Commerce has been using its massive amounts of corporate money to distort American democracy. Let the record show that its foreign affiliates appear to be dead set on doing much worse in foreign countries, even if it means backing a brutal dictator like Mubarak.

TUNISIAN ADMINS SPEAK
http://www.wired.com/dangerroom/2011/01/as-egypt-tightens-its-internet-grip-tunisia-seeks-to-open-up/
As Egypt Tightens Its Internet Grip, Tunisia Looks to Open Up
by Mike Elkin / January 28, 2011
When Zine El Abidine Ben Ali’s dictatorship began unravelling here last month amid violent street protests, the Tunisia’s Internet administrators saw a massive spike in the number of sites placed on government block lists. But, in contrast to the embattled Egyptian government, the Ali regime never ordered Internet and cellphone communications shut off or slowed down, the head of the Tunisian Internet Agency says. “I think Ben Ali did not realize where the situation was going or that he could be taken down,” Tunisian Internet Agency (ATI in its French initials) director Kamel Saadaoui tells Wired.com. “Maybe if he had known that he would have cut the Internet. But the number of blocked sites did grow drastically when the revolution started. They were trying desperately to block any site that spoke about Sidi Bouzid. In a few weeks the number doubled.”
Egypt’s blackout, confirmed Thursday by Internet monitoring company Renesys, shut down four out of five of the country’s ISPs, with one connection left open to Noor Group, which hosts the Egyptian stock exchange, Rensys reported. The move signals an unprecedented clampdown on communications interference as activists, apparently inspired by Tunisia’s successful uprising, are taking to the streets in massive numbers. During its 15-year existence, the ATI had a reputation for censoring the Internet and hacking into people’s personal email accounts. All Tunisian ISPs and email flowed through its offices before being released on the Internet, and anything that the dictatorship of Ben Ali didn’t like didn’t see the light of day.
Saadaoui, its director of three years, complains that the perception of the ATI as an oppressive cyber-nanny is undeserved. He was just following the regime’s orders, he insists. Now that the government has changed, he’s following those new policies, helping open up Tunisian Internet access as never before. “We are computer and electronic engineers, not policemen,” Saadaoui says at his office in the ATI headquarters, a handsome, white bungalow near Pasteur Square in a high-end neighborhood of Tunis. “We don’t check email and we don’t filter websites, even though we have filtering engines on our network. We run the engines technically, but we don’t decide to block your blog. We don’t even know you have a blog. But,” he adds, “we give access to these engines to other institutions that have been mandated by the government to choose which websites should be blocked. They have the gateway that has all the mail to be read.” In other words: don’t blame us. We just work here.
Saadaoui described the governmental oversight of the Internet as an encrypted interface built and maintained by the ATI. Only the government can manipulate it. “We gave them an interface where they can go in and add anything they want to block,” he says. “We don’t even know what they were banning because the list is encrypted. We can only see the number of blocked sites and some other technical aspects, such as CPO load, how much traffic… things like this. Sometimes we learn about the blocked sites when people call in and ask why their blog has been blocked. Then we know.” At first, the regime banned around 300 websites, but as Internet use grew throughout the country – from 1 percent of the population in 2000 to 37 percent as of last November – the blacklist bloated to more than 2,000. When the government started going after proxies, Saadaoui said, the number jumped to many thousands. He estimated that around 1,000 of the blocked sites were political, and the rest were proxies.
The revolution began on December 17, when a 26-year-old fruit vendor named Mohammed Bouazizi in the central Tunisian town of Sidi Bouzid set himself on fire to protest the humiliating tactics of local officials. The suicide jolted Tunisians; they began to protest in the streets — and clash with police. Around 100 people died throughout the country. The media, controlled by Ben Ali’s advisers, reported only that criminals were looting. But videos of the protests, riot police and their victims appeared on Facebook and bloggers began reporting the daily events with first-hand accounts, photographs and videos. This information helped drive the uprising, and the government responded by allegedly hijakcing Tunisian Facebook passwords. At the same time, hackers began to attack the Tunisian government’s control over the Internet. They bombed the ATI’s DNS and website, and tried to bomb the email centipede gateway. The National Computer Security Agency, which fights hacking, phishing, viruses and fraud, took on the activists who tried to overload government websites with Distributed Denial of Service attacks. “When the hackers did DDOS they did a good job, and Anonymous did a good job,” Saadaoui says, smiling. “But not on everything. They weren’t able to take down the DNS, they weren’t able to take down the main servers or the network, but they were able to DDOS websites. They were able to bomb Ben Ali’s website.”
Open, But Uncertain Future
Since Ben Ali fled the country on January 14, the transitional government has removed several restrictions on Internet use while the 60-person ATI aims to focus on tasks more befitting an Internet regulator: providing bandwidth and IP numbers, DNS management, IP addresses, research and development, electronic commerce, and web hosting. The agency is also the ISP for all public institutions. How the dictator-less Tunisia will rebuild its Internet architecture is still being discussed, Saadaoui says. But one optimistic sign is that 33-year-old blogger and activist Slim Amamou, who was arrested during the revolt, is now the secretary of state for youth and sports. The Ministry of Communications and Technology has announced that anyone who has a SMTP server can have direct access to the Internet without going through the governmental post office.
The interface that allows the government to block sites, however, still exists. Saadaoui promises that it will be used only to block pornography, child pornography, nudity and “hate,” using URL classifiers. “The new government told us to keep the filtering engines where they are and to allow them to add categories that they don’t like,” Saadaoui says. “The difference now is that they will ask a judge to approve the filtering. The problem is not filtering, the problem is who filters and based on what law. Before, people would filter without applying the law, and now we will filter with a judicial mandate. And the current mandate is to block pornography, pedophilia, nudity, and hate.” Many Tunisians, such as Amamou and the hackers who fought the ATI during the revolution, prefer a completely open Internet. Saadaoui disagrees. He says the current filters are necessary on a political level: “The limits are symbolic. It’s a message from the government that we are a Muslim and conservative society and that we would appreciate if you didn’t go to these [filtered] sites. Besides, Saadaoui says, everyone knows how to sidestep the restrictions, anyway. “Tunisia has a lot of young, open people who know how to go around filters via hotspot proxies,” he says. “So really it’s useless to block. Whatever we do, there are ways to get around it.”
CHOKE POINTS in the CLOUD
http://www.theatlantic.com/technology/archive/11/01/tunisia-egypt-miami-the-importance-of-internet-choke-points/70415/
Tunisia, Egypt, Miami: The Importance of Internet Choke Points
by Andrew Blum / Jan 28 2011
The news yesterday evening that Egypt had severed itself from the global Internet came at the same time as an ostensibly far less inflammatory announcement closer to home. Verizon, the telecom giant, would acquire “cloud computing company” Terremark for $1.4 billion. The purchase would “accelerate Verizon’s ‘everything-as-a-service’ cloud strategy,” the press release said. The trouble is that Terremark isn’t merely a cloud computing company. Or, more to the point, the cloud isn’t really a cloud.
Among its portfolio of data centers in the US, Europe and Latin America, Terremark owns one of the single most important buildings on the global Internet, a giant fortress on the edge of Miami’s downtown known as the NAP of the Americas. The Internet is a network of networks. But what’s often forgotten is that those networks actually have to physically connect — one router to another — often through something as simple and tangible as a yellow-jacketed fiber-optic cable. It’s safe to suspect a network engineer in Egypt had a few of them dangling in his hands last night. Terremark’s building in Miami is the physical meeting point for more than 160 networks from around the world. They meet there because of the building’s excellent security, its redundant power systems, and its thick concrete walls, designed to survive a category 5 hurricane. But above all, they meet there because the building is “carrier-neutral.” It’s a Switzerland of the Internet, an unallied territory where competing networks can connect to each other. Terremark doesn’t have a dog in the fight. Or at least it didn’t. Verizon insists there’s nothing to worry about. Terremark will be set up as a wholly owned subsidiary. Its carrier-neutral status will remain. “We’re not going to try to cramp their style at all,” said Lowell McAdam, President and COO of Verizon. “There will be no moves to take certain customers out of play.”
I can’t help but think of it in the context of another recent purchase. Earlier this month, Google bought its New York office building, 111 8th Avenue, for a reported $1.9 billion. As the Wall Street Journal described, “about one third of the space is occupied by telecommunications companies.” But that’s severely understating the situation: 111 8th is another of the most important buildings on the Internet, on a short list of fewer than a dozen worldwide. Like the NAP of the Americas, it houses hundreds of independent networks, scattered across the office spaces of multiple independently owned sub-landlords. And now Google owns the whole thing. One assumes that they’re not going to cramp their style either. “It’s not about the ‘carrier hotel’ space,” said Google Senior Vice President Jonathan Rosenberg. “We have 2,000 employees on site. It’s a big sales center, but also a big engineering center. With the pace at which we’re growing, it’s very difficult to find space in New York. There are very few buildings in New York that can accommodate our needs. This gives us a lot of control over growing into the space.” But on a day when a government to 80,000,000 managed to find the Internet’s “kill switch,” it’s worth remembering that the Internet is a physical network. It matters who controls the nodes. With these two deals, Google and Verizon may have chipped away at the foundation walls of an open, competitive–and therefore free — Internet.

U.S. SENATORS PROPOSE INTERNET KILL SWITCH
http://www.techamerica.org/cybersecurity-bill-strengthens-government-industry-cooperation-but-new-regulations-would-carry-unintended-consequences
http://news.cnet.com/8301-13578_3-20007418-38.html
Senators propose granting president emergency Internet power
by Declan McCullagh / June 10, 2010
A new U.S. Senate bill would grant the president far-reaching emergency powers to seize control of or even shut down portions of the Internet. The legislation announced Thursday says that companies such as broadband providers, search engines, or software firms that the government selects “shall immediately comply with any emergency measure or action developed” by the Department of Homeland Security. Anyone failing to comply would be fined. That emergency authority would allow the federal government to “preserve those networks and assets and our country and protect our people,” Joe Lieberman, the primary sponsor of the measure and the chairman of the Homeland Security committee, told reporters on Thursday. Lieberman is an independent senator from Connecticut who caucuses with the Democrats. Because there are few limits on the president’s emergency power, which can be renewed indefinitely, the densely worded 197-page bill (PDF) is likely to encounter stiff opposition.
TechAmerica, probably the largest U.S. technology lobby group, said it was concerned about “unintended consequences that would result from the legislation’s regulatory approach” and “the potential for absolute power.” And the Center for Democracy and Technology publicly worried that the Lieberman bill’s emergency powers “include authority to shut down or limit Internet traffic on private systems.” The idea of an Internet “kill switch” that the president could flip is not new. A draft Senate proposal that CNET obtained in August allowed the White House to “declare a cybersecurity emergency,” and another from Sens. Jay Rockefeller (D-W.V.) and Olympia Snowe (R-Maine) would have explicitly given the government the power to “order the disconnection” of certain networks or Web sites.
On Thursday, both senators lauded Lieberman’s bill, which is formally titled the Protecting Cyberspace as a National Asset Act, or PCNAA. Rockefeller said “I commend” the drafters of the PCNAA. Collins went further, signing up at a co-sponsor and saying at a press conference that “we cannot afford to wait for a cyber 9/11 before our government realizes the importance of protecting our cyber resources.” Under PCNAA, the federal government’s power to force private companies to comply with emergency decrees would become unusually broad. Any company on a list created by Homeland Security that also “relies on” the Internet, the telephone system, or any other component of the U.S. “information infrastructure” would be subject to command by a new National Center for Cybersecurity and Communications (NCCC) that would be created inside Homeland Security. The only obvious limitation on the NCCC’s emergency power is one paragraph in the Lieberman bill that appears to have grown out of the Bush-era flap over warrantless wiretapping. That limitation says that the NCCC cannot order broadband providers or other companies to “conduct surveillance” of Americans unless it’s otherwise legally authorized. Lieberman said Thursday that enactment of his bill needed to be a top congressional priority. “For all of its ‘user-friendly’ allure, the Internet can also be a dangerous place with electronic pipelines that run directly into everything from our personal bank accounts to key infrastructure to government and industrial secrets,” he said. “Our economic security, national security and public safety are now all at risk from new kinds of enemies–cyber-warriors, cyber-spies, cyber-terrorists and cyber-criminals.”
A new cybersecurity bureaucracy
Lieberman’s proposal would form a powerful and extensive new Homeland Security bureaucracy around the NCCC, including “no less” than two deputy directors, and liaison officers to the Defense Department, Justice Department, Commerce Department, and the Director of National Intelligence. (How much the NCCC director’s duties would overlap with those of the existing assistant secretary for infrastructure protection is not clear.) The NCCC also would be granted the power to monitor the “security status” of private sector Web sites, broadband providers, and other Internet components. Lieberman’s legislation requires the NCCC to provide “situational awareness of the security status” of the portions of the Internet that are inside the United States — and also those portions in other countries that, if disrupted, could cause significant harm. Selected private companies would be required to participate in “information sharing” with the Feds. They must “certify in writing to the director” of the NCCC whether they have “developed and implemented” federally approved security measures, which could be anything from encryption to physical security mechanisms, or programming techniques that have been “approved by the director.” The NCCC director can “issue an order” in cases of noncompliance.
The prospect of a vast new cybersecurity bureaucracy with power to command the private sector worries some privacy advocates. “This is a plan for an auto-immune reaction,” says Jim Harper, director of information studies at the libertarian Cato Institute. “When something goes wrong, the government will attack our infrastructure and make society weaker.” To sweeten the deal for industry groups, Lieberman has included a tantalizing offer absent from earlier drafts: immunity from civil lawsuits. If a software company’s programming error costs customers billions, or a broadband provider intentionally cuts off its customers in response to a federal command, neither would be liable. If there’s an “incident related to a cyber vulnerability” after the president has declared an emergency and the affected company has followed federal standards, plaintiffs’ lawyers cannot collect damages for economic harm. And if the harm is caused by an emergency order from the Feds, not only does the possibility of damages virtually disappear, but the U.S. Treasury will even pick up the private company’s tab.
Another sweetener: A new White House office would be charged with forcing federal agencies to take cybersecurity more seriously, with the power to jeopardize their budgets if they fail to comply. The likely effect would be to increase government agencies’ demand for security products. Tom Gann, McAfee’s vice president for government relations, stopped short of criticizing the Lieberman bill, calling it a “very important piece of legislation.” McAfee is paying attention to “a number of provisions of the bill that could use work,” Gann said, and “we’ve certainly put some focus on the emergency provisions.”

